Linkedin Access to your account has been restricted – Final debrief and resilience plan
2024 May 30th, cruising along the internet, doing my posts, sending some contacts invites, and giving shit to the #clowd as usual (cloud=leak, connected=hacked). Damn, no public cloud for anything else than public data. Please.
Did my morning routine, and went for lunch. Checked my phone, and an email from linkedIn came in :
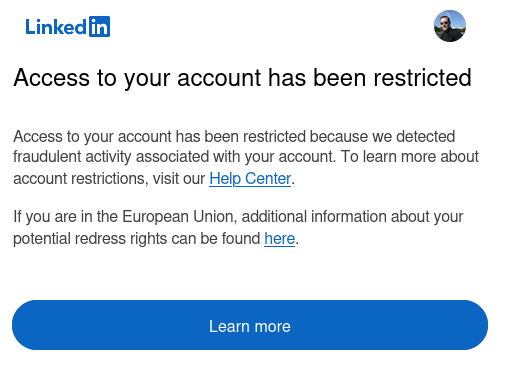
I read this, and I’m like, hell, someone tried to hack my account ! And I even feel thankful that LinkedIn actually protected my account from this fraudulent activity ! … You know, I rant against the cloud, I point security issue hoping people avoid them, I collaborate, share awareness and do things for good. (I don’t want my private data to leak from the cloud, or anyone else’s data either).
I want security and privacy by default and by design. So I wrap my lunch and go on the computer.
Try to login to figure what the hell (is this that PDF that a random guy sent me for review ? Did it steal my oauth session ? … all this kind of things cross my mind. When you are sharing a lot of strong opinions like me, you always have bunch of haters ).
And that’s the screen I get :
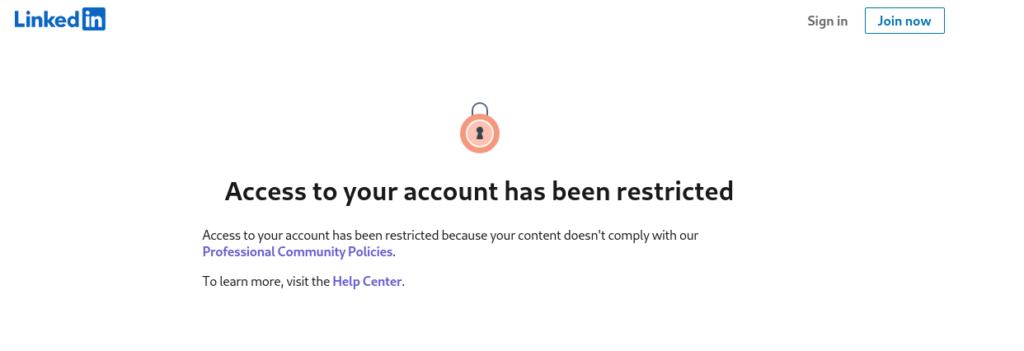
I read this, especially the part that says « your content doesn’t comply with our Professional Community Policies », and then I’m like, WTF is this ! Double check the rules, nah, nothing really. Doesn’t make sense.
So I’m like, I’ll wait a bit, I assume I’m just logged out. Check LinkedIn help, but when you are logged out like this, you can’t access much !
I start to get paranoid, I think I really annoyed the cloud gods (M$), or maybe it was that post that I made, about Quebec government who was about to waste billions of dollar in this shitty public cloud mixing Azure and AWS… but I didn’t make it up, it was just highlighting public info from main stream article (I’m always careful, only share information from known sources, despite all the tips and disclosure I receive, I’m careful, avoiding lawsuits and liability).
Part of my company activity is managing LinkedIn pages for other businesses, Cyber Security firms, and others. I also post brand partnership content, like the amazing Cynomi company, which I also use for my vCISO work. Being locked out, I can’t deliver my engagement (writing content, posting on their behalf)…
I try to login again, same BS « content doesn’t comply with our… », can you tell WTF you didn’t like ? nope, they won’t.
I start to search online, and I realize that this is happening to bunch of people, which I never realized (I’ve been shadow banned, but I could still access my content, not this time), and I found this : https://expandi.io/blog/linkedin-account-restricted/
Again, I wonder what did I do wrong ? I get hooked to « too many connection requests », true that, I sent dozens of them in the past week, to CISOs, CSOs, CIOs… you know, getting more insight, and visibility.
I let this go for the night and hope that next day stuff is resolved, after submitting many support requests on LinkedIn public help pages. These are frustrating because when you post/submit the form, you get redirected to a related topic, and get no confirmation whatsoever, no email, nothing.
Next day I ask my buddies on signal if they still see me, nope… ask other buddies, not only they don’t see me, but our chats are now showing a warning, that malicious content was sent to them (almost looking as a criminal), although it shows « linkedin member », with difference warnings, the softer like this one :
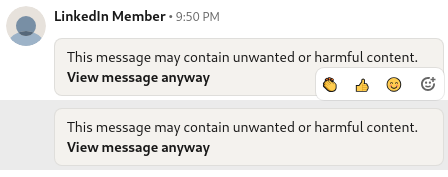
And for some others, a red warning, or black warning.
I think, the worse is that you have NO IDEA WHY ! You don’t know what you did wrong.
I know tons of LinkedIn people, I did mentorship, I’ve been invited to record LinkedIn courses (which I didn’t have time to at the time), yet, we did interviews. As LinkedIn top voice in 2020, they verified my ID, sent me a hoodie from LinkedIn, with a thank note (hell they know where I live). It’s not like if they don’t know me.
I verified my ID, I’m cleared for some sensitive things too, government and linkedin knows it all.
But at this point, I realize that I didn’t keep most of the info out of LinkedIn. My speaking engagement history, my certifications, all of this, no track !
At the same time, I still try to figure what did go wrong, what did I do ! Was it a sponsored link that I forgot to check as « brand partnership » ? …. to be banned like this, it must be serious (well it’s not ! )
Thankfully, some communication happened by email, and some key contact swho invited me to events where I actually had lunch at the table with LinkedIn infra management and others !! (damnit, we are connected on LinkedIn, but not outside), well, the person that got me as guest, is in my inbox.
I email him, and it starts ! What I didn’t know is that LinkedIn has been wiping people like this for a while, and that it has gone totally nuts. My friend is so pissed, he sends email to Linkedin CEO, and head of trust and safety. At the same time, I start to receive emails from partners and friends.
People have no idea why you disappear, and you have no way to tell them, no I didn’t die, I didn’t kill myself. Some of you know, second half of 2023, I went in bad bad burn out, chronic stress and anxiety, and I did stay offline for a few months.
One of my partner send me this beautiful email :
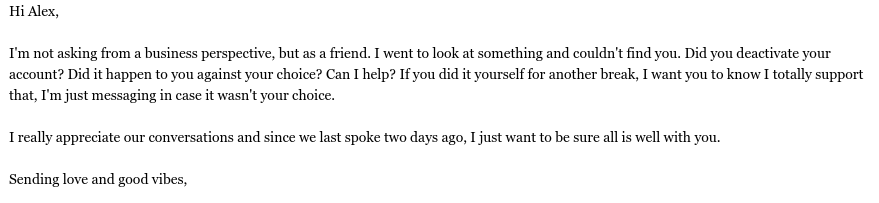
(the type of kindness that get some tears in my eyes, in adversity, true people shine, and some other show they are real fuckers)
Feeling support from your business partners, friends, and network is critical as you are deleted from the professional world. Let’s say it, LinkedIn is where business connects, if you’re forced out, that’s over. I know other platforms exist, but business and job, that’s LinkedIn (for now).
Then it escalates, my partners from all over the world who work WITH linkedin, reach out to their contacts. I’m also member of many groups, one of them being Hackers Without Borders. People that do good and help others.
As soon as they heard about it, they kicked in, coordinated response, they had to fight big corporations before for abuses, these guys are no kids. The team coordinate and start a public communication campaign. (I know a LOT of people, I helped big organizations, countries, governments, law enforcement, and others, I mean, I’d never bug them for favor, unless it’s becoming critical, I could have escalated, way more).
They started to post this « Alexandre Blanc missing » picture :
I gave the group as many contact names as I could remember. I did borrow the account of someone else, to browse some key contacts of mines, and help my memory to spot other people I was connected to.
Basically, the ones I have, from top of my head, direct discussions with. At the same time, I avoided customers, as much as doable, not to mix the situation.
And my buddies tag them in the post, then it started to blast ! People reaching out by email, on my blog here, as I did post about my deletion here.
Email started to get in, my twitter account started to receive messages, I started to be in CC with escalation all over. Specialist of social media account recovery kicked in.
I received support basically from all over the world, anywhere I gave conferences, webinar or brought value, they’ve shown support. From Malaysia to India, from Europe to USA, from Israel to the Emirates ! All over the planet, thousands.
Lawyers practices, activists, joined, lawyers and legal council speaking about coordinating class action, activists reaching to politics about the abuses of big tech. It was about to blow in the media, due to the lobbying groups, and contacts. A shit storm bigger than me.
I felt a bit scared, because it was way bigger than me. I didn’t control the response anymore.
A social media specialist gave me this URL, telling me, that’s the one with which they got success to recover accounts in such situation : https://www.linkedin.com/help/linkedin/ask/TS-RHA
Keep this handy, it seems one of the most relevant page, if you tried all the other forms, as help pages are not easy to find when you are locked out.
On June 8th, at noon 10 days after I got kicked out, I received an email from LinkedIn customer support as follow :
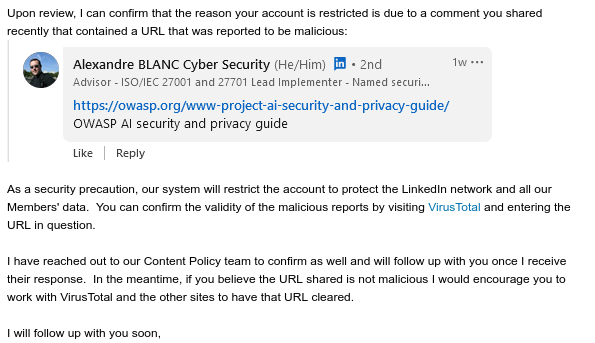
First, after all the scenario and hypothesis that came to mind, everything I did read online, it was just that ?!!!!
I was like WTF, can’t you just hide the post for the time of the review ? (it did happen before, they’d tell you that post visibility is limited to you due to bla bla bla with a specific post) but locking me out 100%, a verified identity, linkedin top voice, because one link came at risk (and it was a false positive), what are you smoking ?!!!!
30 min later, I receive this email :
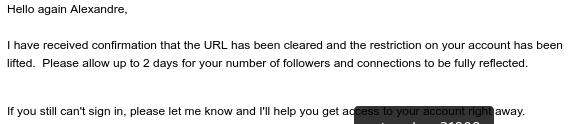
So, you tell me, that you deleted my account, blocked my business, make me appear as a criminal to all my contacts who looked for messages, because of a false positive !! Are you kidding me ?
Not only this, but it takes 2 days to restore everything, so that’s 12 days of business loss (as content creator and social media service provider) !!! 12 DAYS !
I know I’m lucky, because dozens of people reached out, in the same situation, some are still locked out, after weeks, some months ! I complain about 12 days, but the platform killed many businesses with its erratic behavior and fake positives.
Key aspects to consider here when you are « restricted » :
- You better keep your contacts out of this platform, make sure you have a good old address book
- You better keep a copy of all your content, profile, articles, etc, on an external platform (I’ve my speaking engagement history that was stored in an article, I didn’t have it anywhere else), same thing with my profile / bio.. only up to date was on linkedin.
- You better keep another, if not many other platforms active, like X. I know it’s not better, but this is where people, businesses, have accounts for most. You have to be where people are.
- Then for sure you should have a mastodon account, and ideally, your own blog, on your own server, with your own backups.
- You should make sure you keep your key contacts on signal / telegram. When getting in touch with people, I never want to bug them or disturb, and I’m most of the time shy to even ask for a phone number (I don’t like when people call me either :P you know, geek :P ). But hell, you need to keep this information.
- You should be part of communities outside of linkedin, signal groups, I don’t know, FSF, EFF, and others, making sure you know people and had even an online call with them. This way, you know who’s who and it’s more easy to get support if need be.
What I’ll do differently from now on ?
- I’ll post both on linkedin AND X (twitter) for redundance
- I’ll keep contact information out of LinkedIn as much as doable (good old email is good enough sometimes)
- I’ll post more on my blog, here, because it’s mine. I can say « shit, fuck, cloud is shit » or any fuckery I want, it’s my stuff. (sorry for swearing, it’s just that I won’t censor myself)
- I’ll trust goodwill a bit more. I tend to be paranoid, but community has been amazing, they gave me hope !
- I’ll learn more and adjust overtime
Did they try to delete me because I’m challenging the public cloud for all its abuses and weaknesses ? what is the real reason behind the suspension ? I really can’t believe an OWASP.org link triggered that.
I think they may have run into a quick BS fake reason, seeing the amount of support growing. I like to think this. I can’t believe it could be as dumb as a false positive. But who knows.
So what’s the resilience plan :
- Make sure you have multiple accounts as admin or content admin on the pages you manage, including your own company
- Make sure you leverage the network you build outside of linkedin
- Make sure you keep multiple channels on multiple platforms (with MFA and all) so as people can reach out
- Keep an active website, or blog, so as you still have a way for others to share the information you want or need.
- Check on your contacts on a regular basis, check your LinkedIn messages, and see who suddenly turned into « LinkedIn Member ». It would be cool to keep an intro message in all conversation with « Hi, I’m firstname, lastname, happy to bla bla bla », so as when the name is deleted, you know who it was.
- Back your linkedin connection with a personal welcome email.
- Ok, it’s late, I’m tired. I may add more later on this. All the best !
![]()
I’m thankful for the support I get in rough time
As you know, while I started my business, and a big part of it involved LinkedIn, from corporate LinkedIn page management (content and growth), to sponsorship and solution partners.
Then my LinkedIn account has been taken down (I have no news whatsoever at this time from LinkedIn – more on it here https://blog.inforeseau.com/2024/05/alexandre-blanc-cyber-kicked-out-from-linkedin ).
Since then, contacts from LinkedIn who wonder what happened to me, reached out showing support, business partners and customers offered tremendous support and flexibility, I can’t be more thankful, and you all give me hope ! (from small businesses to multi billions dollars companies I deal with)
For all of you, who’ve shown flexibility, and business intelligence, because what matters is a win win partnership, thank you.
There is more than tech in all of this, there is humanity. That’s why I fight for privacy and security by design and by default, that’s why I approach things the way I do.
It’s about humanity, it’s not about AI, it’s not about the latest hype crap, it’s about sharing, understanding, learning and supporting.
Thank you all of you, as you know me from linkedin as Alexandre Blanc Cyber Security, as you know my company (Alexandre Blanc Cyber), which funnily I’ve been told is still visible on linkedIn, while I can’t manage it because my LinkedIn account is « restricted » (I can’t login, I can’t access support, basically, I can’t access the platform as myself).
![]()
Cyber security news of the day – 2024 May 31

Cyber security news by Alexandre Blanc Cyber
2024 Friday 31
Here is what you should be aware of today :
BBC Breach Puts 25K Pension Scheme Members at Risk
Though information such as dates of birth, email addresses, and home addresses were compromised, « the Beeb » assures individuals that financial information is still protected. The cloud leaks, as usual, can’t trust systems you don’t own and manage ! #cloud #clowd #cybersecurity
CISA warns of actively exploited Linux privilege elevation flaw
It’s linux patch time !The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has added two vulnerabilities in its Known Exploited Vulnerabilities (KEV) catalog, including a Linux kernel privilege elevation flaw. (Oh by the way, the stupid cloud mostly runs on Linux, so you can just pray that they patch your workloads, otherwise, privilege escalation in shared hosting like public cloud, good luck ! !)
Snowflake compromised? Attackers exploit stolen credentials
Seems that the cloud is leaking and leaking and leaking again ! Have attackers compromised Snowflake or just their customers’ accounts and databases? Conflicting claims muddy the situation.
The linked article share recommendation for Snowflake users to try to reduce the impact of the incident, aside of only praying, as this is the only thing you can do when you use public cloud, and it won’t fix much ! LOL … The cloud is a JOKE !
Another link on this deeply corrupted cloud topic : https://www.bleepingcomputer.com/news/security/snowflake-account-hacks-linked-to-santander-ticketmaster-breaches/
Mysterious Cyber Attack Took Down 600,000+ Routers in the U.S.
This is bad, while LinkedIn and Microsoft are busy blocking account from certified and verified security people like me, the real threat actors are taking down more than half a millions routers in the US ! (I’m a bit pissed, yes)
« More than 600,000 small office/home office (SOHO) routers are estimated to have been bricked and taken offline following a destructive cyber attack staged by unidentified cyber actors, disrupting users’ access to the internet. »
And that’s about it for now ! Thanks in advance for sharing, as I’m now the enemy No 1 on Linkedin :P Feel free to share the news yourself using the share buttons below ! Enjoy !
![]()
Links
Calendrier
| L | M | M | J | V | S | D |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||
Recherche
Derniers articles
Tresronours Twitter
Keywords cloud topic
Membre de la FSF
Liens qui vont bien
Mots clés vrac – keyword cloud
License du contenu – CC By NC SA
Archives
- Getting voLTE on your Android with Fizz and others
- Defining the scope of an ISMS within ISO 27001
- Resumed posting and expanding on X
- Linkedin Access to your account has been restricted – Final debrief and resilience plan
- I’m thankful for the support I get in rough time
- Cyber security news of the day – 2024 May 31
- Alexandre Blanc Cyber Kicked out from Linkedin
- You’ll most likely find me on LinkedIn
- The Russian roulette landing page !
- RTSP, Debian, VLC, not playing, IP Camera
- 5G network hosted in the cloud, no internet, no phone ! So smart ! And I ended on TV, This week in cyber
- They lock the door for privacy… but they keep a copy of the key, and couple of backdoors
- Worst is yet to come, but they all warned you
- Migrating an old WordPress and handling character set, UTF8, latin1, latin1_swedish_ci
- From a broken TLS CA, to Facebook, to FIN12 hit and run
- Yes we can fix this mess, but do we want to ? That’s another story
- Criminals are still dominating the game, why are we doing so wrong, and what can we learn in this tech ocean ?
- Riding cloud can be tricky, don’t fall from it, in the weekly cyber !
- The threat landscape is very dynamic – Cyber news this week
- Cybersecurity is not obvious even for this newsletter !
- Install Slack desktop app on Kali rolling fixing libappindicator3-1 missing dependency
- How to delete all resources in azure to avoid charges after trial on your forced credit card registration
- Proxmox – ZFS – Dead drive on active VM, recover from replicated disk
- Restrict access to proxmox web admin interface
- Migrate your ESXI VMs to proxmox ZFS
- Install your VPN server with pi-hole on OVH VPS in 30 min
- Using raspberry pi 3 as wifi bridge and repeater and firewall
- Raspberry 3 – create a wifi repeater with USB wifi dongle
- raspberry 3 – routeur pare feu point d’acces wifi avec filtrage pub et tracking – router firewall access point with ads and tracking filtering
- Dell XPS 13 touchpad – corriger la sensibilité
- Utiliser Zazeen set top box depuis une connexion videotron
- Fermeture de mon compte facebook – la dernière goutte
- Choisir un kernel par defaut au demarrage de Centos 7.2 – configuration grub2
- Openvpn access server 2.0.25 et android
- Régler la luminosité du laptop par ligne de commande
- chromium outlook web app version complete sous linux
- Nexus 7 2012 – android 5 lollipop solution au probleme de lenteur
- HDD led sur Xubuntu – xfce
- xubuntu 14.04 verrouiller ecran de veille et desactiver mise en veille a la fermeture de l’ecran
- Authentification avec Radmin en utilisant Wine sur Gentoo
- Patcher bash sur une distribution plus supportee comme fedora 11
- Zimbra desktop sous xubuntu 14.04 64bit – fix
- xubuntu 12.10 probleme de son avec VLC – pulse audio – alsa – toshiba L855D – solution
- Evolution sous xubuntu 12.10 – bug affichage a la configuration – solution temporaire
- Booster son acces internet en changeant de DNS pour opendns
- Serveur DLNA sous ubuntu – minidlna
- sshfs sous windows – dokan sshfs
- xubuntu 11.10 Installer le plugin java pour firefox
- Installer Google Earth sur Xubuntu 11.10
- Installer nagios sur Fedora 11 depuis les sources


