Alexandre Blanc Cyber Kicked out from Linkedin
Edit on 2024 June 8th, Saturday, after the involvement and support worldwide, and a pressure from an incredible amount of people, LinkedIn restored my account. They claimed I got banned because I shared a malicious link (this one : Owasp AI and Security Guide ). This is why they deleted me. And then, they claim that after verification, the link was finally not malicious.
As you can guess, it’s a power game, and they wanted to slap me for something they didn’t like. But the power of communities has been stronger. That’s my take. I can’t express how thankful I am for all the support. Love to you all. Will take a few days to get back on track fully.
Edit on Friday night, after finding a great article linked in the comment
(and here) , lately, as I started my own business, I also started to add many connections and sent a lot of requests. The linked article about LinkedIn account restriction explains that adding too many « unknown » people, will lead to this. So, it seems that looking to expand my network, actually killed my network.
Will edit the post if things move, but I think this is it. Too many connection requests sent. (about 30 I’d say)
So, hopefully you’ll learn from this, don’t fuck it up as I just did.
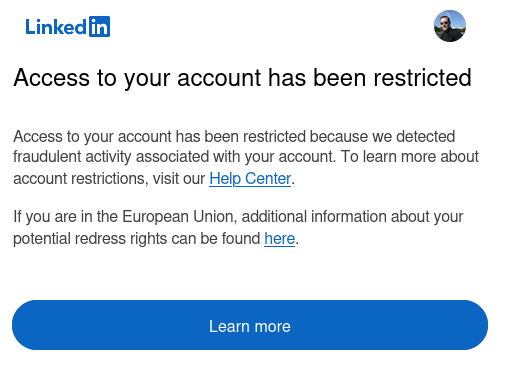
So I got this email, and got blocked on all my devices. I vanished from the platform, my cyber buddies told me they can’t find me anymore.
I obviously had verified ID, MFA, and all available option for security. At this point, when I try to login, I got the following message :
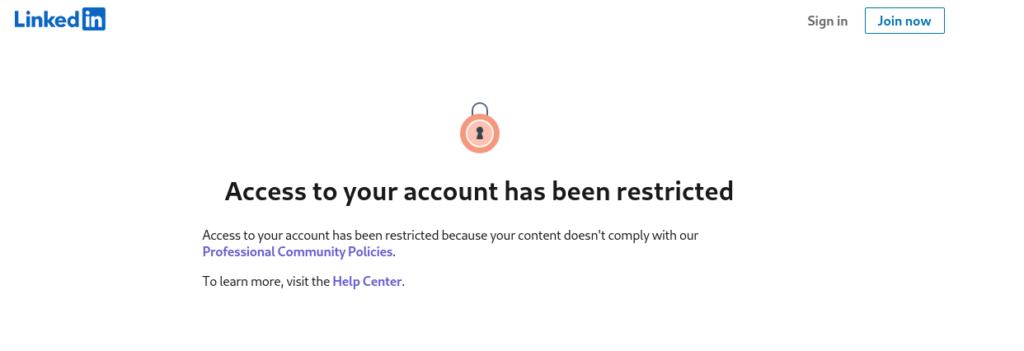
Which is interesting, because I don’t know what this is referring to, and this is not aligned with the email stating « fraudulent activity detected ». Well, I’m known to fight AGAINST fraud. So, that’s about it.
That’s the cloud, after all, I rant a lot about it, you own nothing, you control nothing, well, here is a plain example. No information, no way to know or recover.
I contacted support via the form 2 times, but nothing there. I’ll wait a bit, and then reach out to insiders.
Fun times ! This happened around noon on 2024 May 30th, so far no news. I guess lunch time :D
![]()
11 Commentaires to Alexandre Blanc Cyber Kicked out from Linkedin
Ajouter un commentaire
Links
Recherche
Derniers articles
Tresronours Twitter
Keywords cloud topic
Membre de la FSF
Liens qui vont bien
Mots clés vrac – keyword cloud
License du contenu – CC By NC SA
Archives
- Getting voLTE on your Android with Fizz and others
- Defining the scope of an ISMS within ISO 27001
- Resumed posting and expanding on X
- Linkedin Access to your account has been restricted – Final debrief and resilience plan
- I’m thankful for the support I get in rough time
- Cyber security news of the day – 2024 May 31
- Alexandre Blanc Cyber Kicked out from Linkedin
- You’ll most likely find me on LinkedIn
- The Russian roulette landing page !
- RTSP, Debian, VLC, not playing, IP Camera
- 5G network hosted in the cloud, no internet, no phone ! So smart ! And I ended on TV, This week in cyber
- They lock the door for privacy… but they keep a copy of the key, and couple of backdoors
- Worst is yet to come, but they all warned you
- Migrating an old WordPress and handling character set, UTF8, latin1, latin1_swedish_ci
- From a broken TLS CA, to Facebook, to FIN12 hit and run
- Yes we can fix this mess, but do we want to ? That’s another story
- Criminals are still dominating the game, why are we doing so wrong, and what can we learn in this tech ocean ?
- Riding cloud can be tricky, don’t fall from it, in the weekly cyber !
- The threat landscape is very dynamic – Cyber news this week
- Cybersecurity is not obvious even for this newsletter !
- Install Slack desktop app on Kali rolling fixing libappindicator3-1 missing dependency
- How to delete all resources in azure to avoid charges after trial on your forced credit card registration
- Proxmox – ZFS – Dead drive on active VM, recover from replicated disk
- Restrict access to proxmox web admin interface
- Migrate your ESXI VMs to proxmox ZFS
- Install your VPN server with pi-hole on OVH VPS in 30 min
- Using raspberry pi 3 as wifi bridge and repeater and firewall
- Raspberry 3 – create a wifi repeater with USB wifi dongle
- raspberry 3 – routeur pare feu point d’acces wifi avec filtrage pub et tracking – router firewall access point with ads and tracking filtering
- Dell XPS 13 touchpad – corriger la sensibilité
- Utiliser Zazeen set top box depuis une connexion videotron
- Fermeture de mon compte facebook – la dernière goutte
- Choisir un kernel par defaut au demarrage de Centos 7.2 – configuration grub2
- Openvpn access server 2.0.25 et android
- Régler la luminosité du laptop par ligne de commande
- chromium outlook web app version complete sous linux
- Nexus 7 2012 – android 5 lollipop solution au probleme de lenteur
- HDD led sur Xubuntu – xfce
- xubuntu 14.04 verrouiller ecran de veille et desactiver mise en veille a la fermeture de l’ecran
- Authentification avec Radmin en utilisant Wine sur Gentoo
- Patcher bash sur une distribution plus supportee comme fedora 11
- Zimbra desktop sous xubuntu 14.04 64bit – fix
- xubuntu 12.10 probleme de son avec VLC – pulse audio – alsa – toshiba L855D – solution
- Evolution sous xubuntu 12.10 – bug affichage a la configuration – solution temporaire
- Booster son acces internet en changeant de DNS pour opendns
- Serveur DLNA sous ubuntu – minidlna
- sshfs sous windows – dokan sshfs
- xubuntu 11.10 Installer le plugin java pour firefox
- Installer Google Earth sur Xubuntu 11.10
- Installer nagios sur Fedora 11 depuis les sources



Well, I found this very interesting resource about this situation :
https://expandi.io/blog/linkedin-account-restricted/
Although my situation is still locked, this might help others. A well written and well explained article.
Keep it handy.
Is your account back?
Cheers / Andrew Guzowski
Nope, no news whatsoever. Linkedin decided to destroy my business.
I mean, it’s cloud based, what else to expect !!!
I used to receive tons of spam, phishing and other criminal attempts, and these would NOT be blocked.
But me, a law abiding citizen, premium customer, top voice, nah, let’s destroy him ! That the cloud, supporting crime and destroying businesses.
My crime ? Sent couple of connection requests. No spam, no marketing shit or sales pitch, nothing.
People should realize that’s AI totalitarian style managed.
I wondered why I couldn’t find you on LinkedIn, and fortunately searching finally brought me here. I’m sorry to hear about this and I’m baffled. You had a ton of followers and engagement, and clearly weren’t involved in any fraud. Meanwhile, spam fills my LinkedIn feed and inbox, and they do nothing. WTF?
Yes, same thing on my end, I had tons of spamming, romance scam, foreign state sponsored actors, constant non requested messages and posts from people I NEVER asked for. But these have been going for month, unstopped.
While me, nope. I don’t know. I think I may have pissed someone who got their ego touched, maybe they didn’t like the truth about the danger of public cloud (which is obviously extremely well shown in this situation).
We’ll see where it goes, but I’ll make bunch of changes in the way I do things, and the situation also shows who to trust, and who not to trust either :)
Thanks a lot for reaching out, for now no news, but some of my partners reached out to internal linkedin team during the weekend, we’ll see how this goes. Yet, I’ve a LOT of learning from this situation, both from resilience standpoint, on the trust (or no trust) side, and also learning a lot from different people. I’ll adjust in the future.
Thanks for commenting and checking on me, highly appreciated.
So, I found this reading, which match my situation as well, same thing, I also use Linux as my main operating system (also use and android and a macbook, but my main machine is linux, for years).
https://medium.com/@lukesdupont/linkedin-is-banning-and-alienating-users-for-no-apparent-reason-4ae81778eda5
Not giving me hope reading this one.
Yet another post about this :
https://www.linkedin.com/pulse/how-lift-linkedin-account-ban-9-tips-from-experienced-alex-ivakhnenko
This is very very terrible, reading this I’m afraid I won’t get my account again, which is just crazy, that’s years of work, building connection, audience, 75K followers, newsletter with 45K subscribers, this would be pure evil.
Alexandre, not absolute here, but may have the reason.
Some hostile, were publishing posts to then hostile links.
IN DOING THAT, they added the @name to the posts, to then once posted DELETE those with an edit so they were no longer « visible » in that post.
(You would see yourself « mentioned » in a post to when there not see yourself « mentioned » in this case)
*OTHERS BEWARE OF THE POST WHEN YOU SEE THIS HAPPEN
Those persons actions, resulted in a filter looking for those « hooking » potential victims in, via this, and where, SOMEONE « writing the filters » that automagical CLOWD FILTER, screwed up.
THUS, (if you did refer to others with an @name for them and post, to then think « Oops » and edit delete them, YOUR BEHAVIOR to an AI, would « look » like that potentially, of the hostile behavior it is looking for.
SAME, as the day HR called me in to say, « your online behavior while on the network is questionable! ».
Yeah, I know that since I am the one responsible for setting UP the system that is to TELL YOU THAT, and also maintaining it, SO IT TELLS YOU THAT, which means I have to attempt access to things that are to BE BLOCKED, to test if they are which then GENERATES the report you are referring TO,,,
OH!
Told her: *PS: YOU WENT TO THE SITE YOU ARE THINKING YOU WILL WRITE ME UP « FOR », POST THAT REPORT, WHICH IS ITSELF A VIOLATION,,, WRITE YOURSELF UP AND SIGN IT!
Other option Alexandre, YOU « MAY » have « Accidentally » posted a link to an article from a (sometimes hostile) site that served the LinkedIN system that parses those links to create the SHORT LINK, a site, that served them « malware or a browser exploit ».
You « may » have run a PEN test against a system where not WHITELISTED to then have your IP, Device, FLAGGED as « hostile » to then be crowd source added to a « LIST » that feeds into a Control at LinkedIN and resulted in you being BLOCKED.
Key point and important is that « YOUR DEPENDENCY » and or « Anyone’s », on a CLOUD CENTRIC « SERVICE », is literally, contrary to, and a perfect example of the accuracy in your statements made ON said service.
Connected = BLOCKED (at the whim of an AI),,,
Hi Brian, thanks for the input. Yes it could be many things, but it would be dumb for a system to blame users that get tagged in anything as we don’t have a hand on this.
I’m aware of the behavior of some threat actor that would post something like « the cloud sucks so much », then tag, get people to comment like « I agree so much with you » and then change the original post to something nasty, and making you look like you support nasty things.
One would hope for some integrity, as a change of meaning of a post should trigger a revision or removal of comments to protect integrity of people take on things.
It is very possible that a link to a safe article turned into corrupted target over time (that a basic phishing detection bypass, sending friday a safe link through shortener to pass the filter, and on monday, threat actors edit redirection to nasty targets so as the victim get tricked). Yet again, with all this AI crap and all, if they can’t achieve basic security it’s scary (how about a warning line, « since this link has been shared, target has been modified, caution ») or something like this.
And yes, perfect illustration of the issue with cloud, owning nothing, controlling nothing. I’m thankful I kept a lot of things out of linkedin, but in the future, if they re activate my account, I’ll pull a lot of things out, it’s way way way too risky to keep anything that you can’t be deprived of (like the article where I kept all my speaking engagement history) and more.
I’ve always been wary of relying on a platform for hosting my content. While they have their uses for marketing, it seems wise to keep all of one’s content backed up and possibly consider not putting all one’s eggs in one basket.
Absolutely agreed. The day to day info feed, marketing and whatever is ok, but the key content, article, and actual contacts should definitely be backed up in a properly owned channel, not clowd.