Install your VPN server with pi-hole on OVH VPS in 30 min
Prereqs : You must have an SSH client (native Linux SSH command, or putty on windows… poor you), you must know how to edit a file in command line (using vim or nano, as you like), you must know how to use terminal menu (tab to switch options, space to select, enter to validate)
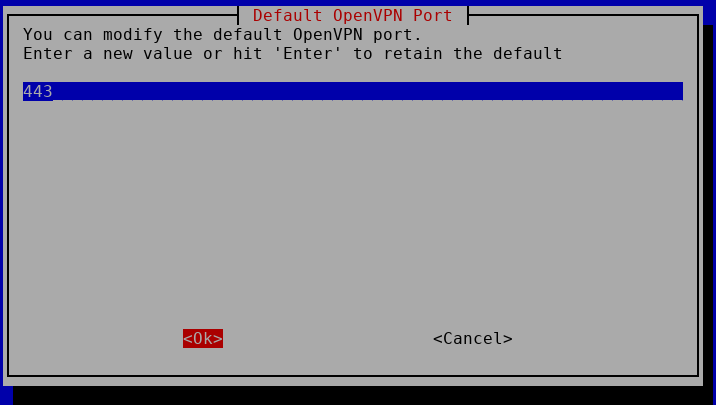
Port : This tutorial expect to run Openvpn on port 443 (SSL port), if you want to use another one, just replace 443 by the port you wish in the whole tutorial below.
Note : This is done using an OVH VPS, with Debian 9, other cloud VPS might differ if not default debian 9.
Note2 : This will allow all devices on VPN to communicate with each other (client to client options enabled by default, and firewall rules allows this as well) – If you want to block client to client communication, check this pagehttps://blog.inforeseau.com/openvpn-and-pihole-on-ovh-vps-server-faq
Order OVH VPS with latest Debian (VPS SSD, cheapest at CAD $4.49/month ! )
SSH to it. (credentials for SSH root in the email you receive after OS installation)
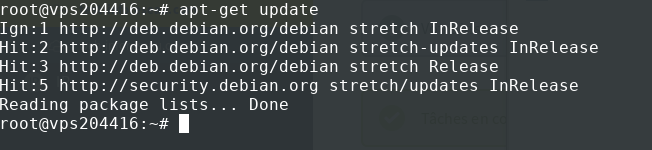
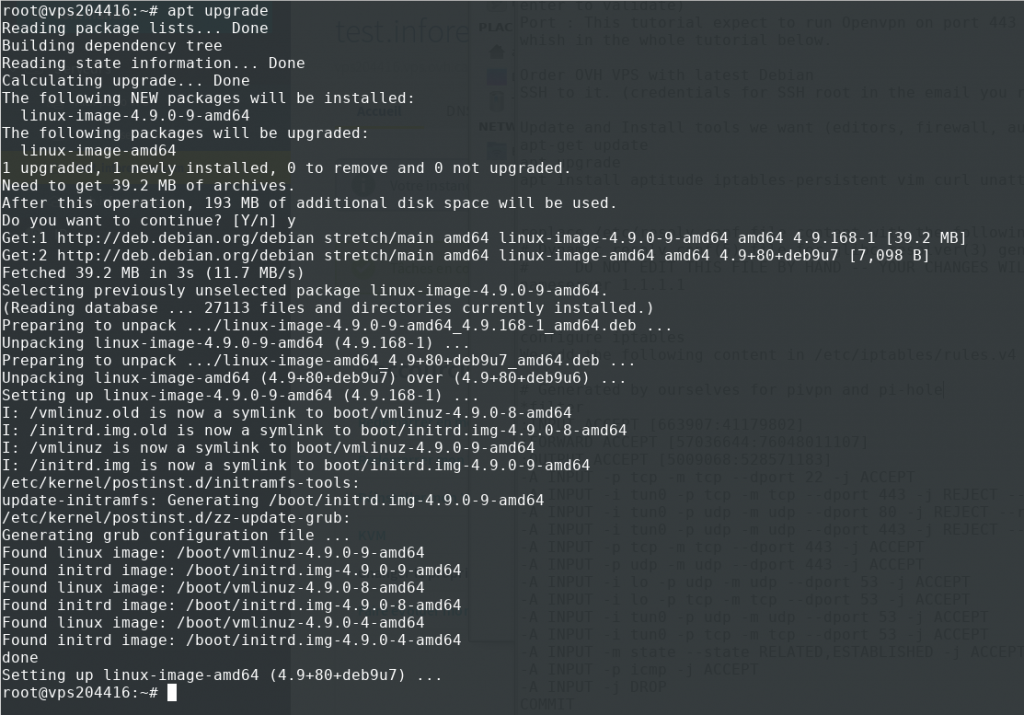
Update and Install tools we want (editors, firewall, auto updates) :
apt-get update
apt upgrade
apt install aptitude iptables-persistent vim curl unattended-upgrades
It should look like this :
(YES to save current IPv4 rules and YES to save current IPv6 fules when install iptables)
Replace /etc/resolv.conf file content with the following
#Dynamic resolv.conf(5) file for glibc resolver(3) generated by resolvconf(8)
#DO NOT EDIT THIS FILE BY HAND -- YOUR CHANGES WILL BE OVERWRITTEN
nameserver 9.9.9.9
Configure iptables
We add the following content in /etc/iptables/rules.v4 (replace all the content using vim or another tool or remotely with filezilla)
#Generated by ourselves for pivpn and pi-hole
*filter
:INPUT ACCEPT [663907:41179802]
:FORWARD ACCEPT [57036644:76048011107]
:OUTPUT ACCEPT [5009068:528571183]
-A INPUT -p tcp -m tcp --dport 22 -j ACCEPT
#Don t change the port 443 in the 3 lines below, this is for pihole performance
-A INPUT -i tun0 -p tcp -m tcp --dport 443 -j REJECT --reject-with tcp-reset
-A INPUT -i tun0 -p udp -m udp --dport 80 -j REJECT --reject-with icmp-port-unreachable
-A INPUT -i tun0 -p udp -m udp --dport 443 -j REJECT --reject-with icmp-port-unreachable
#End of don t change these
#Port allowed for VPN, change if you decide to use another port for your VPN server (replace 443 below by whatever you chose)
-A INPUT -p tcp -m tcp --dport 443 -j ACCEPT
-A INPUT -p udp -m udp --dport 443 -j ACCEPT
#End of port to change if you get your VPN server to run on another port
-A INPUT -i lo -p udp -m udp --dport 53 -j ACCEPT
-A INPUT -i lo -p tcp -m tcp --dport 53 -j ACCEPT
-A INPUT -i tun0 -p udp -m udp --dport 53 -j ACCEPT
-A INPUT -i tun0 -p tcp -m tcp --dport 53 -j ACCEPT
-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -p icmp -j ACCEPT
-A INPUT -j DROP
COMMIT
#Completed on Sat Apr 27 16:18:39 2019
#Generated by iptables-save v1.6.0 on Sat Apr 27 16:18:39 2019
*nat
:PREROUTING ACCEPT [496992:46323248]
:INPUT ACCEPT [335723:24234770]
:OUTPUT ACCEPT [486171:32444728]
:POSTROUTING ACCEPT [491702:32816107]
#if you need to use 1 or more other port(s), just add as many line as below, whitout the # so it is actually loaded, ens3 is the NIC of the VPS, adjust if yours differ
#Below will allow to connect to port 8080 aside of 443.
#- A PREROUTING -i ens3 -p udp -m udp --dport 8080 -j REDIRECT --to-port 443
COMMIT
#Completed certainly after 2019 Apr 27t
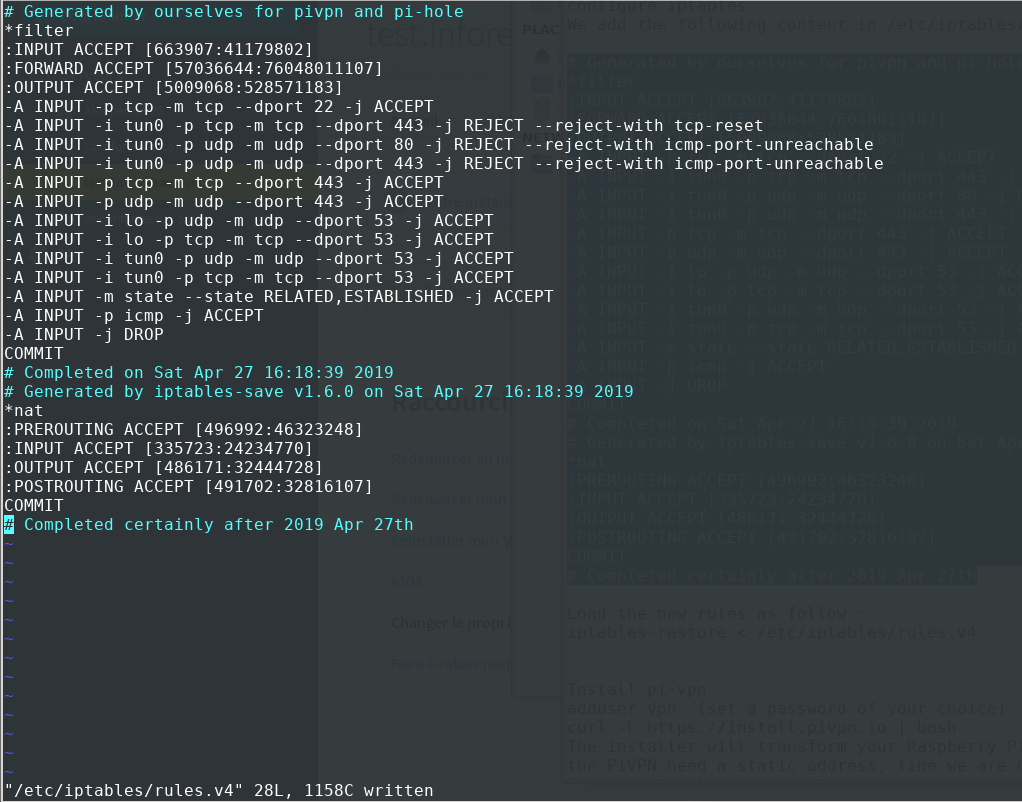
Load the new rules as follow :
iptables-restore < /etc/iptables/rules.v4
Install pi-vpn
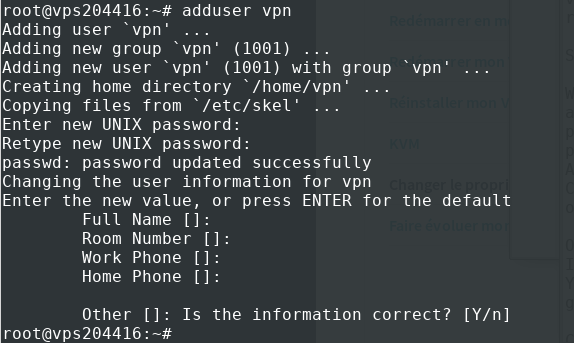
adduser vpn (set a password of your choice)
curl -L https://install.pivpn.io | bash
(if you have a name resolution issue, type the command again until it moves on)
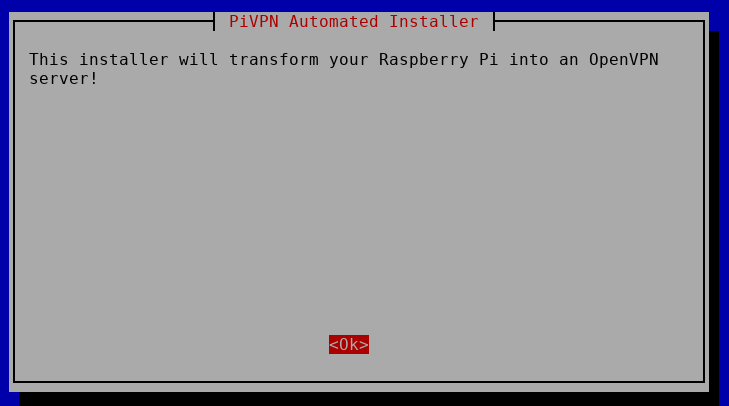
The installer will transform your Raspberry Pi into an openvpn server (will do for your debian VPS too :P ) OK
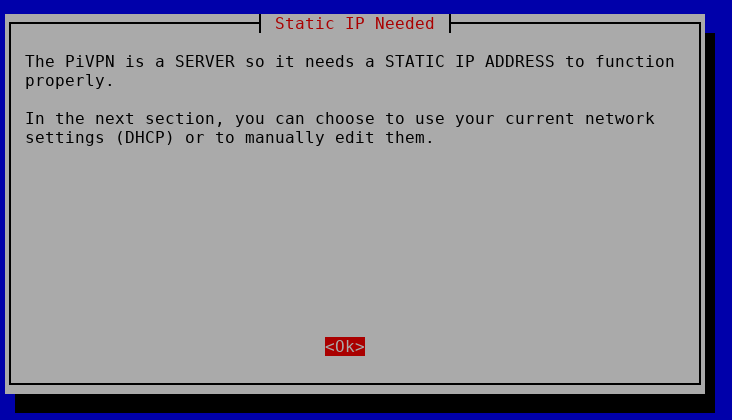
the PiVPN need a static address, fine we are on VPS with assigned IP, OK
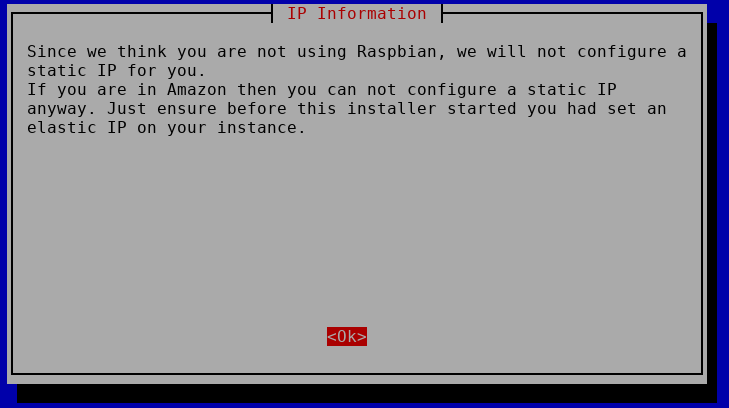
Since we think you are not using raspbian… correct, fine, OK
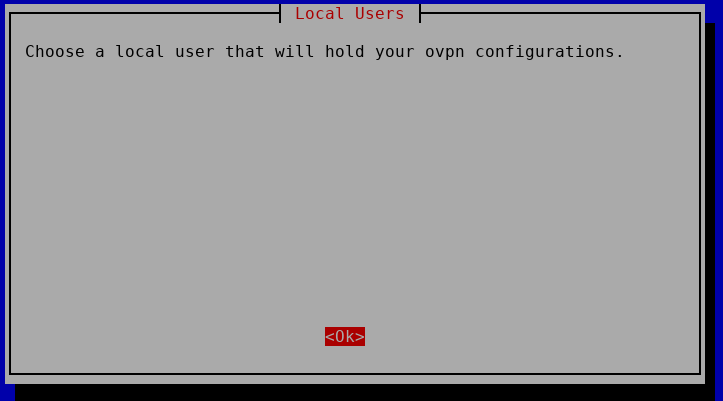
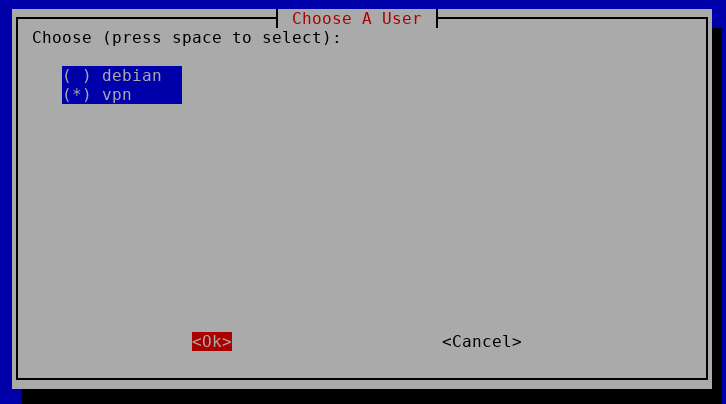
Choose user OK, select « vpn » that we just created and OK
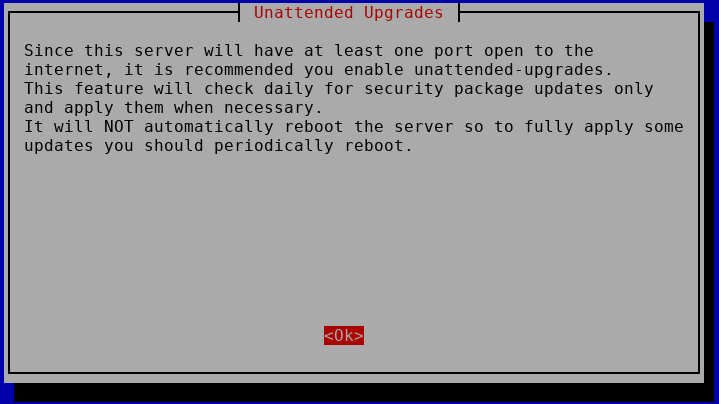
It is recommended that you enable « unattended upgrade », OK, we already did this at the beginning
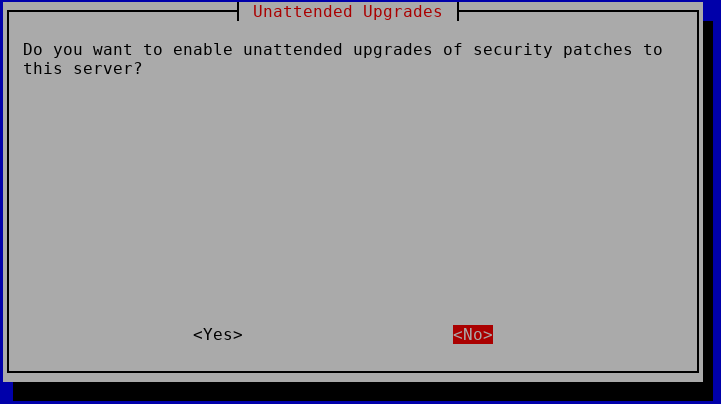
Do you want to enable unattended upgrades of security : NO (it is already done, no need to redo)
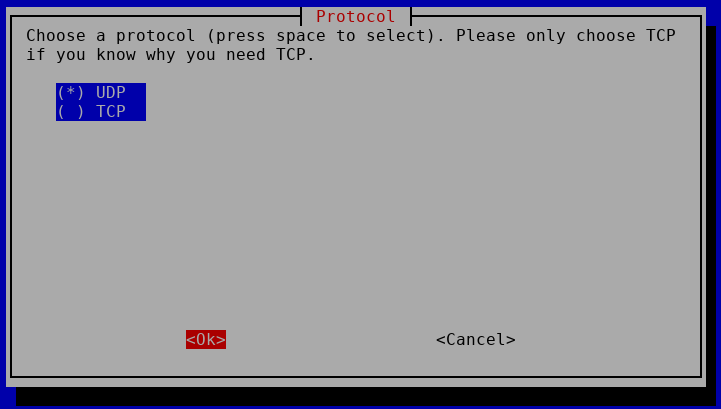
We want to use UDP protocol, Select UDP and OK
We modify the port to 443 as this will most likely will be allowed on most networks and OK
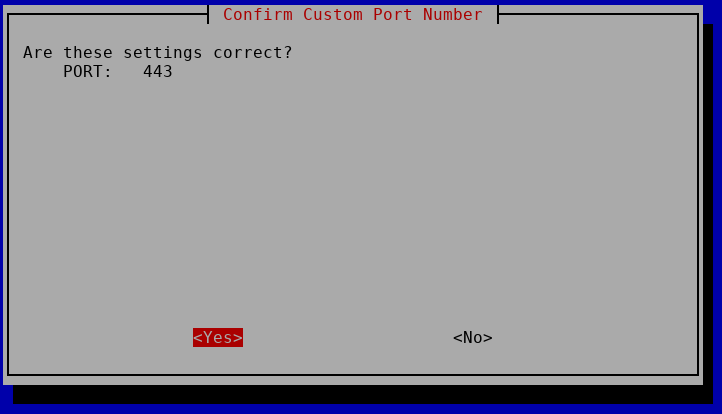
Are these settings correct : YES
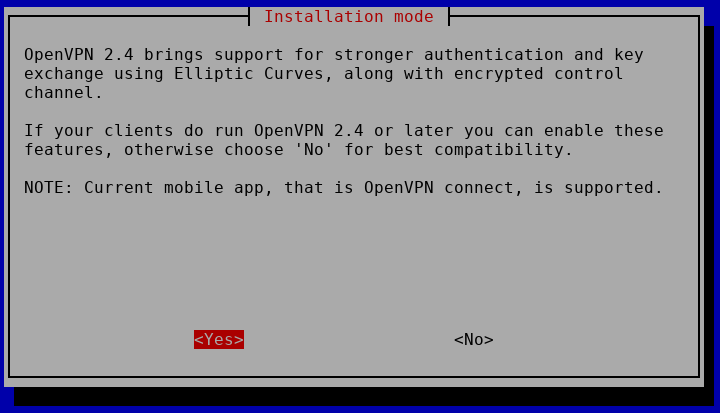
YES to the next screen about Elliptic curves for key exchanges
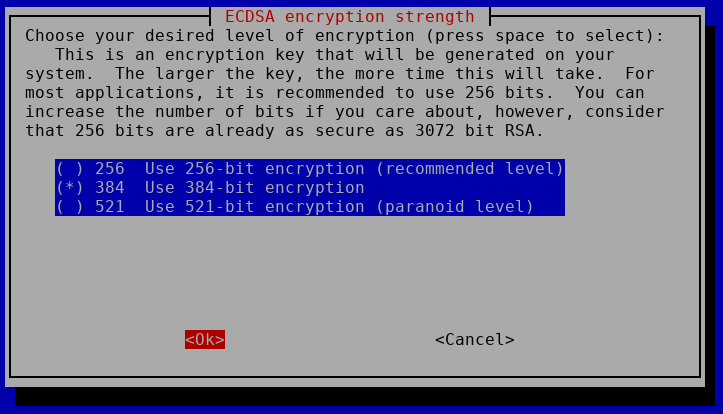
Next, i’d recommend at least 384-bit encryption, safer, not crazy overhead. OK
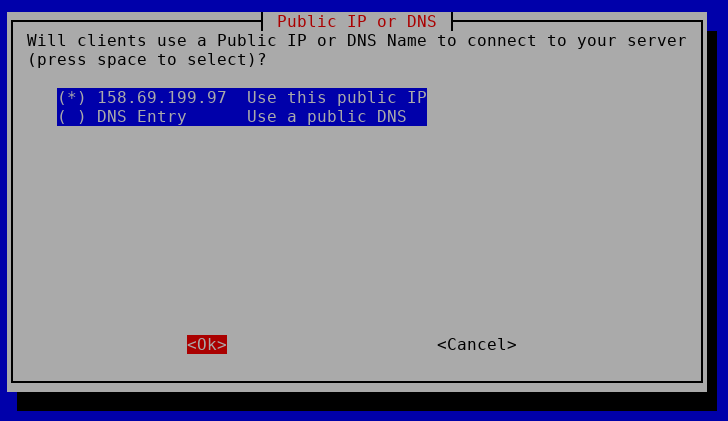
Client can use the public IP, OK, this is totally fine as VPS has static IP (DNS is more useful in case of dynamic DNS use) – It should be the IP of YOUR VPS
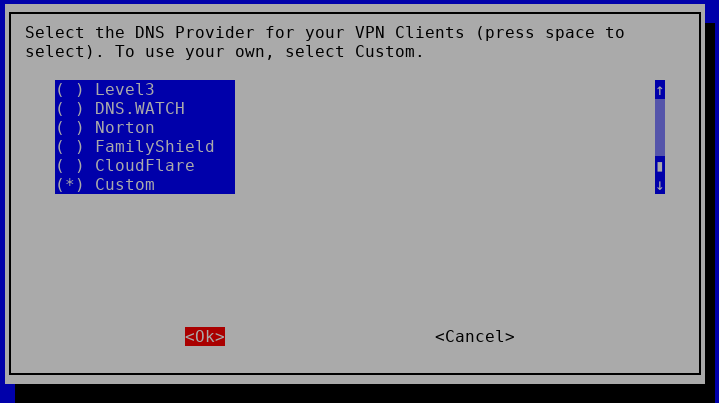
Select DNS provider, this is a key point, we want the benefit of pi-hole on our VPN, so we’ll go down the list, and select « Custom » (go down with arrows on keyboard to select custom), then OK
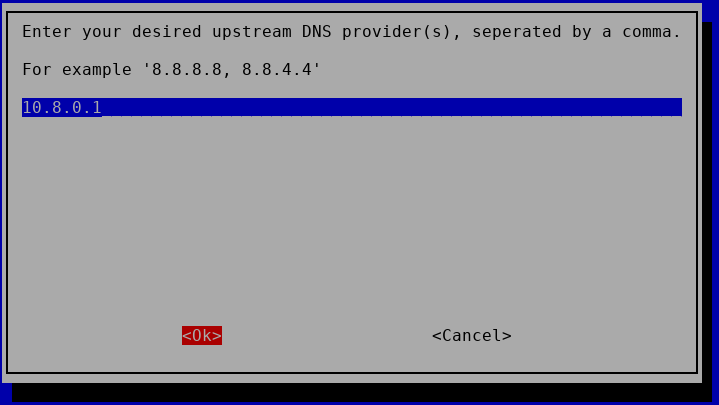
Fill the info with 10.8.0.1 and OK (this will be the IP of the openvpn server on tap0 that we allowed in firewall)
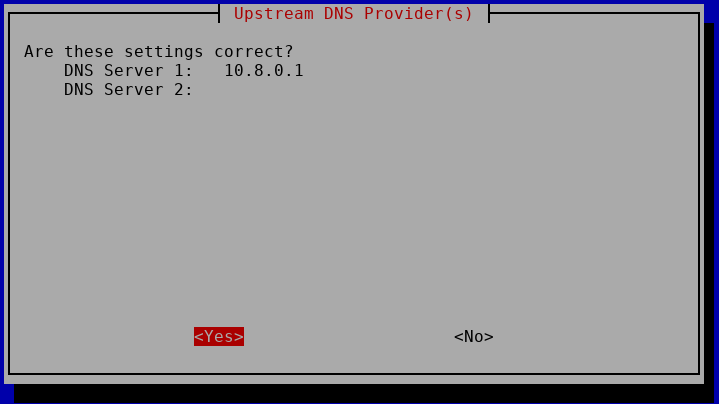
Are these settings ok ? YES
validate the end of installation OK
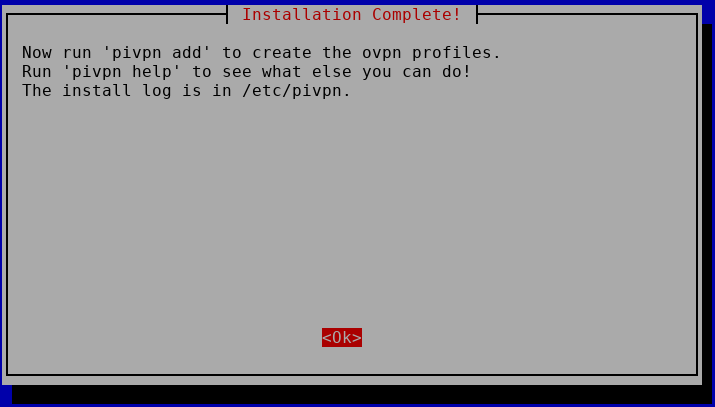
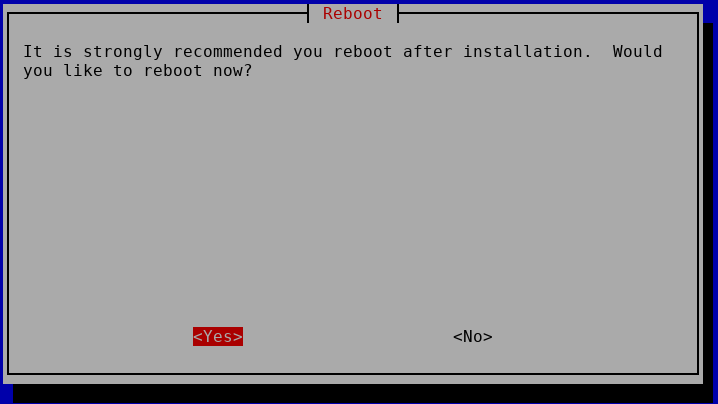
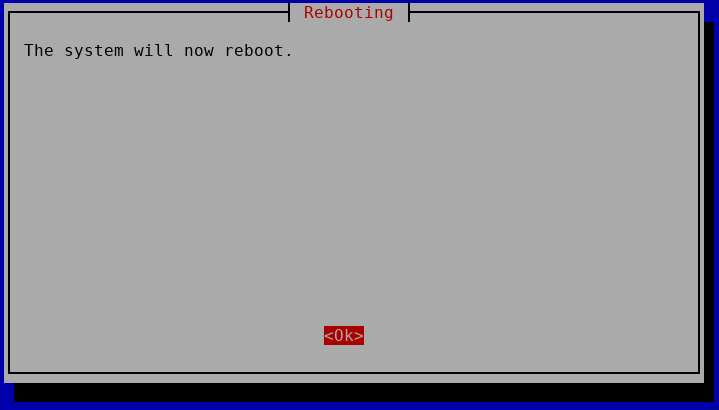
reboot the VPS – YES and confirm OK
After reboot, SSH again on it
We’ll generate a client certifacte
as root :
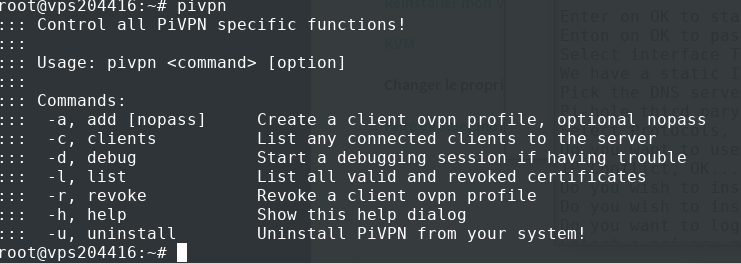
pivpn -a
provide a client name (like device name such as myphone1) and a password.
As shown, the client ovpn file will be placed in /home/vpn/ovpns/ (since we use the user « vpn » to handle VPN).
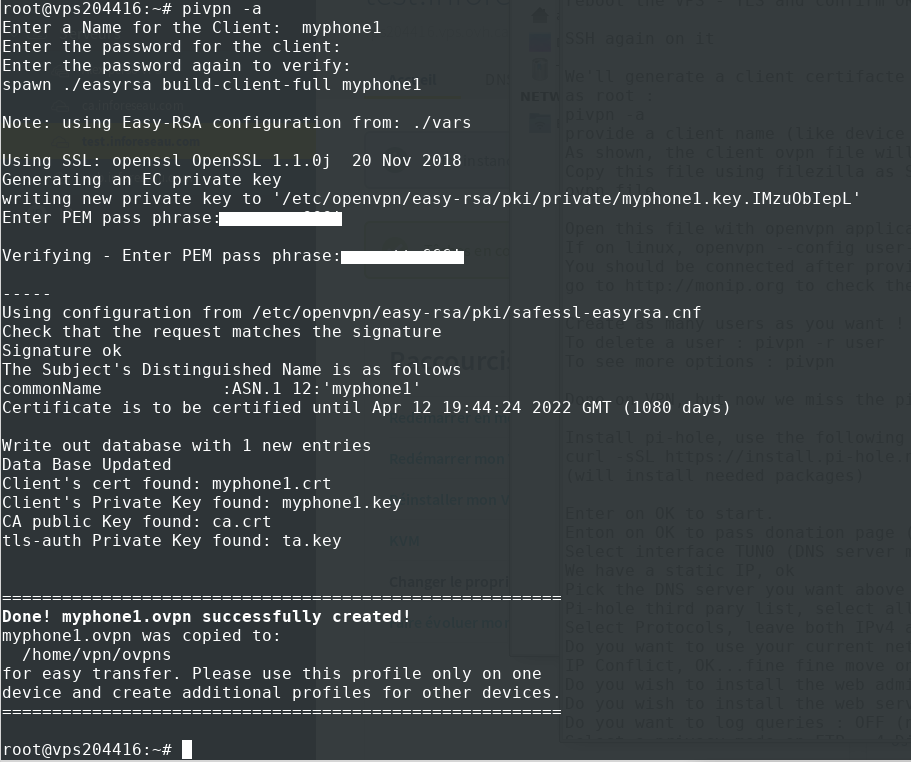
Copy this file using filezilla via SFTP(SSH) or cat on ovpn (cat /home/vpn/ovpns/user-you-chose.ovpn) and copy the content to a local ovpn file.
Open this file with openvpn application on your phone and connect :D
If on linux,
openvpn --config user-you-chose.ovpn
and it will connect.
You should be connected after providing the chosen password used when creating VPN user, and surf internet (when pi-hole below is installed too :P ) from your VPS with pi-hole filtering enabled !
go to http://monip.org to check the IP seen by websites (it should be the IP of your VPS).
Create as many users as you want ! Yes it’s free !
To delete a user : pivpn -r user
To see more options : pivpn
Done on VPN, but now we miss the pi-hole DNS filtering service, here we go (otherwise DNS resolution and filtering won’t work)
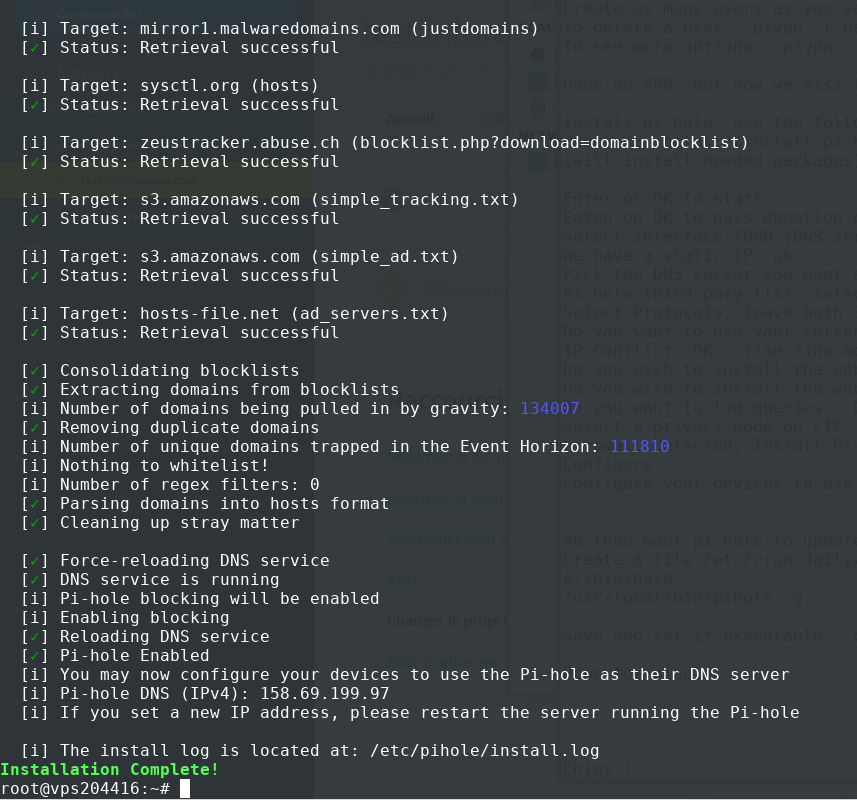
Install pi-hole, use the following command :
curl -sSL https://install.pi-hole.net | bash
(will install needed packages)
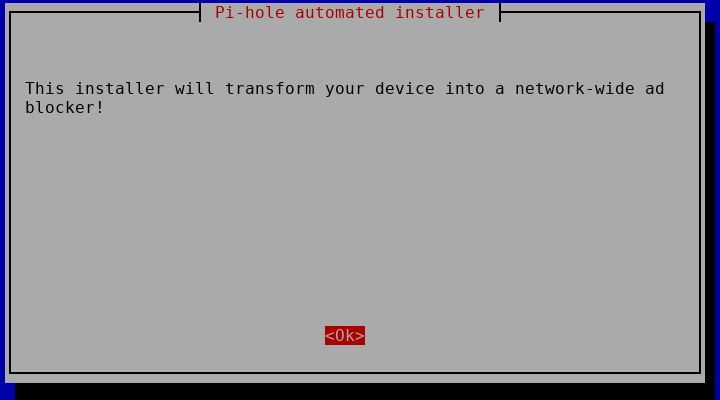
Enter on OK to start.
Enter on OK to pass donation page (donate if you want to support pihole project, it is amazing)
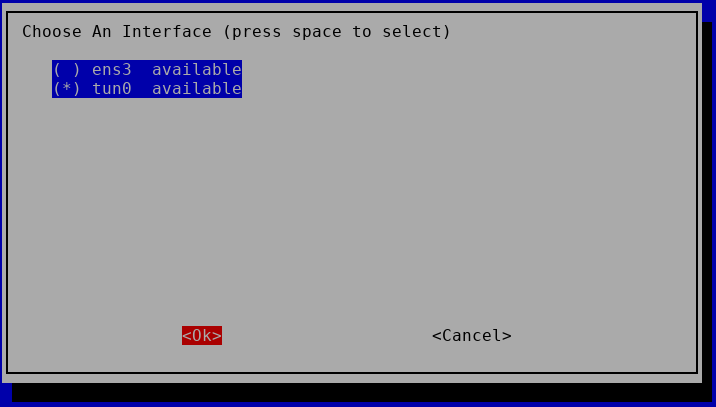
Select interface TUN0 (DNS server must listen on VPN interface)
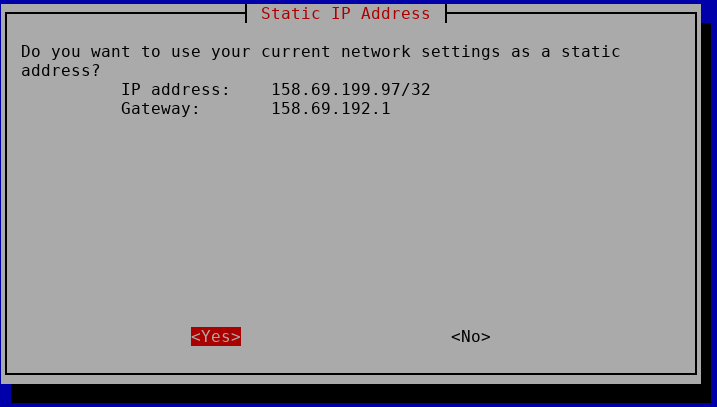
We have a static IP, ok
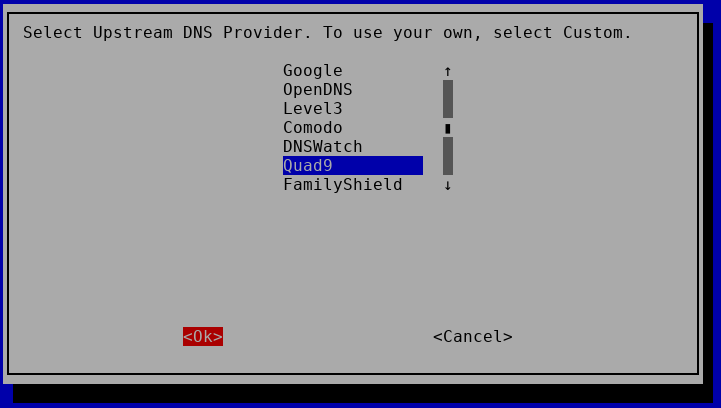
Pick the DNS server you want above pihole (i pick Quad9, but anything is good as you like) and press ok
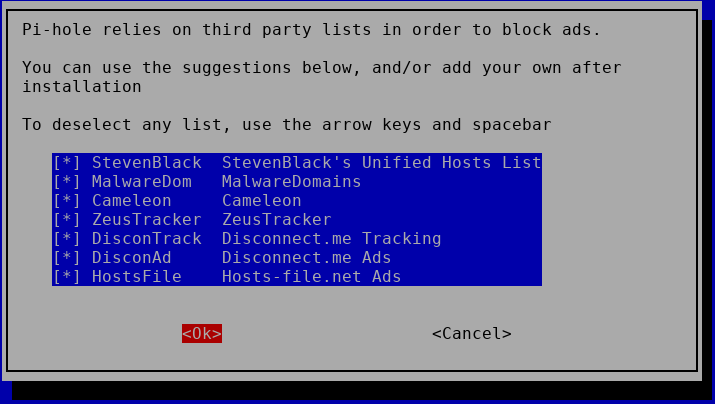
Pi-hole third party list, select all and press OK
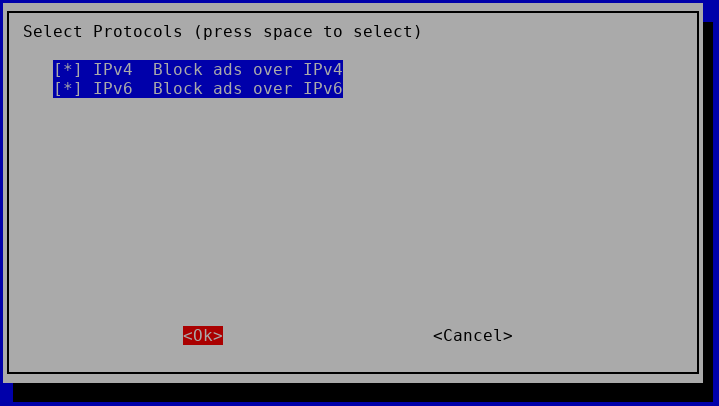
Select Protocols, leave both IPv4 and IPv6 checked, OK
Do you want to use your current network settings, YES ! ( This should show the IP of YOUR VPS)
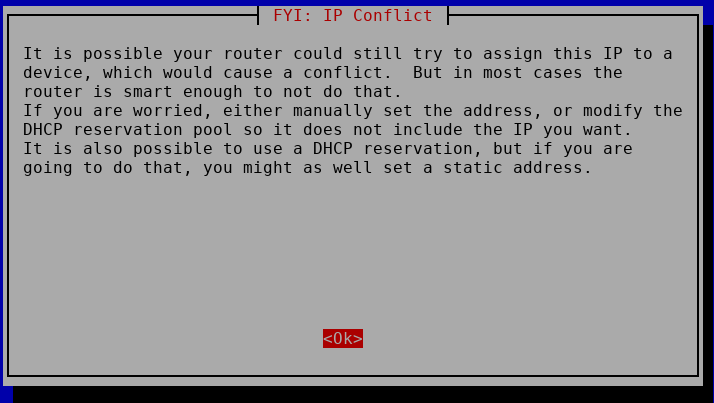
IP Conflict, OK…fine fine move on :P
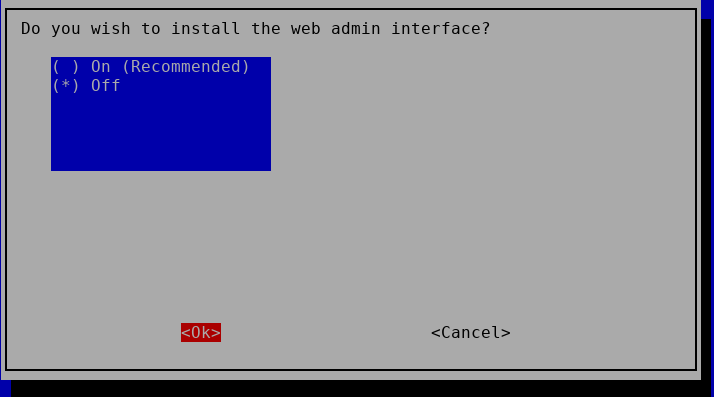
Do you wish to install the web admin interface : OFF and OK (we don’t need it, we won’t connect to it, won’t open it)
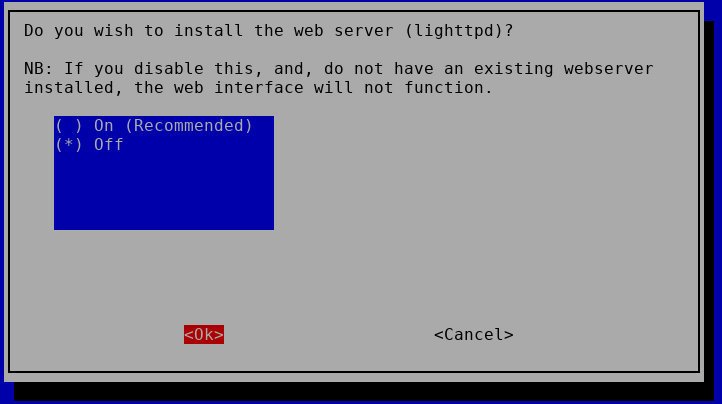
Do you wish to install the web server (lighttpd) ? OFF and OK (not needed)
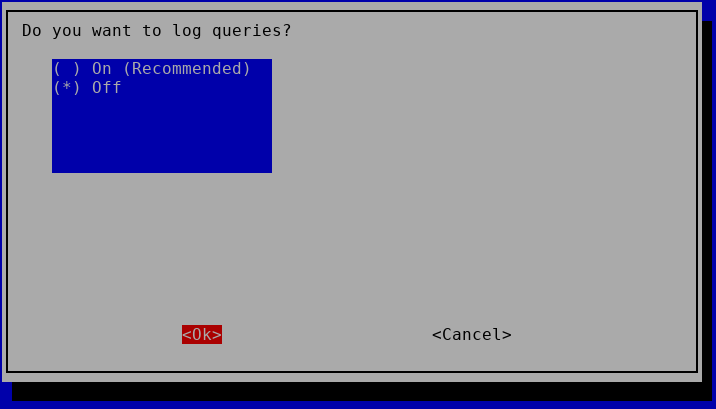
Do you want to log queries : OFF (no we don’t want to leave tracks…)
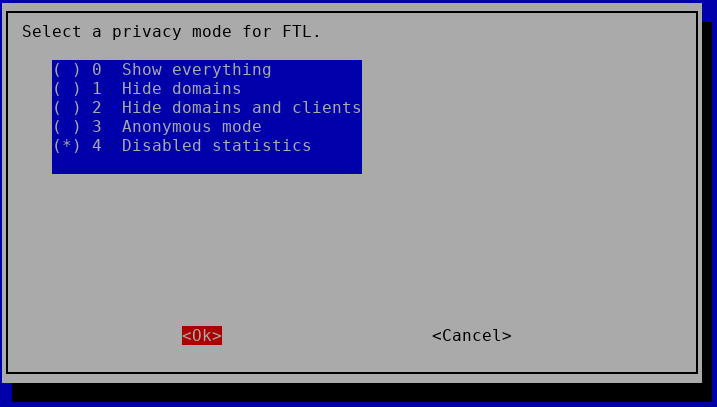
Select a privacy mode on FTP : 4 Disabled statistics (we are all about privacy here)
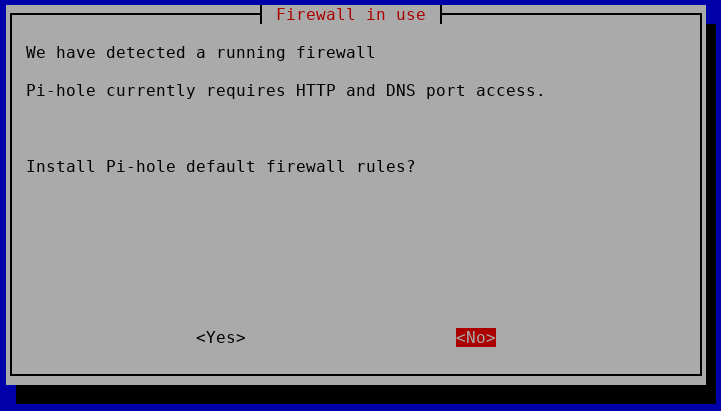
Firewall Detected, Install Pi-hole default firewall rules? NO, they are already in the iptables rules we copied
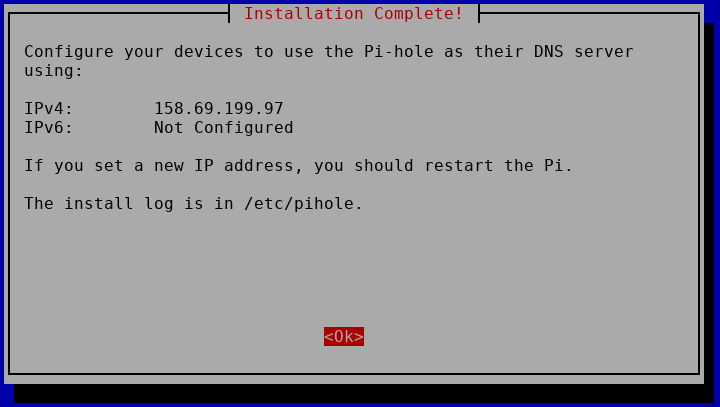
Configure your devices to use the pi-hole…. OK, we’ll do this in VPN config after.
We then want pi-hole to update its blacklist automatically everyday.
Create the file /etc/cron.daily/piholeupdate with the following content :
#!/bin/bash
/usr/local/bin/pihole -g
Save and make it executable :
chmod +x /etc/cron.daily/piholeupdate
Done for pihole.
Enjoy !
Use the command « pivpn » to generate as many users as devices you have, install openvpn client on it (android, iOS, linux or windows or tunnelblick on MAC), and import the .ovpn file that you generated using the password you entered when creating user.
If one of your device is stolen or lost, revoke the certificate.
You can now browse internet, seen as your VPS, and no one can snoop on your traffic, without adds, without tracking :P (still take a canvas randomizer plugin for your browser to avoid device signature).
Security note : By default the OVH VPS is installed with a ROOT account and a password provided to you. Online servers are under attack on a permanent basis.
I recommend that you log on your VPS with an SSH private/public key instead of the password.
To do this, you need to generate a private/public key on your client machine (on linux, usually located in /home/your_user/.ssh/id_rsa.pub). If you have one, you can use it otherwise, generate one with the command « ssh-keygen -t rsa », then you copy the content of your local file id_rsa.pub to your VPS in the file /root/.ssh/authorized_keys)
Then try to ssh to the machine, ssh root@your_server, accepting he signature, you should be logged in without password
Now that we can SSH without password, we’ll disable the password authentication in SSH server. Edit the file /etc/ssh/sshd_config, and add the following line (if not already set) :
PasswordAuthentication no
Save and quit, restart the sshd server : service sshd restart
From this point, you can no longer login with a password, only the SSH key is accepted.
No more dictionary attack or password guessing. If ever you lose your local machine/private key, you can always go in the OVH console,through web management interface, and open the vKVM, to connect on the machine through the console with the root password. Enjoy.
![]()
3 Commentaires to Install your VPN server with pi-hole on OVH VPS in 30 min
Ajouter un commentaire
Links
Calendrier
| L | M | M | J | V | S | D |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||
Recherche
Derniers articles
Tresronours Twitter
Keywords cloud topic
Membre de la FSF
Liens qui vont bien
Mots clés vrac – keyword cloud
License du contenu – CC By NC SA
Archives
- Getting voLTE on your Android with Fizz and others
- Defining the scope of an ISMS within ISO 27001
- Resumed posting and expanding on X
- Linkedin Access to your account has been restricted – Final debrief and resilience plan
- I’m thankful for the support I get in rough time
- Cyber security news of the day – 2024 May 31
- Alexandre Blanc Cyber Kicked out from Linkedin
- You’ll most likely find me on LinkedIn
- The Russian roulette landing page !
- RTSP, Debian, VLC, not playing, IP Camera
- 5G network hosted in the cloud, no internet, no phone ! So smart ! And I ended on TV, This week in cyber
- They lock the door for privacy… but they keep a copy of the key, and couple of backdoors
- Worst is yet to come, but they all warned you
- Migrating an old WordPress and handling character set, UTF8, latin1, latin1_swedish_ci
- From a broken TLS CA, to Facebook, to FIN12 hit and run
- Yes we can fix this mess, but do we want to ? That’s another story
- Criminals are still dominating the game, why are we doing so wrong, and what can we learn in this tech ocean ?
- Riding cloud can be tricky, don’t fall from it, in the weekly cyber !
- The threat landscape is very dynamic – Cyber news this week
- Cybersecurity is not obvious even for this newsletter !
- Install Slack desktop app on Kali rolling fixing libappindicator3-1 missing dependency
- How to delete all resources in azure to avoid charges after trial on your forced credit card registration
- Proxmox – ZFS – Dead drive on active VM, recover from replicated disk
- Restrict access to proxmox web admin interface
- Migrate your ESXI VMs to proxmox ZFS
- Install your VPN server with pi-hole on OVH VPS in 30 min
- Using raspberry pi 3 as wifi bridge and repeater and firewall
- Raspberry 3 – create a wifi repeater with USB wifi dongle
- raspberry 3 – routeur pare feu point d’acces wifi avec filtrage pub et tracking – router firewall access point with ads and tracking filtering
- Dell XPS 13 touchpad – corriger la sensibilité
- Utiliser Zazeen set top box depuis une connexion videotron
- Fermeture de mon compte facebook – la dernière goutte
- Choisir un kernel par defaut au demarrage de Centos 7.2 – configuration grub2
- Openvpn access server 2.0.25 et android
- Régler la luminosité du laptop par ligne de commande
- chromium outlook web app version complete sous linux
- Nexus 7 2012 – android 5 lollipop solution au probleme de lenteur
- HDD led sur Xubuntu – xfce
- xubuntu 14.04 verrouiller ecran de veille et desactiver mise en veille a la fermeture de l’ecran
- Authentification avec Radmin en utilisant Wine sur Gentoo
- Patcher bash sur une distribution plus supportee comme fedora 11
- Zimbra desktop sous xubuntu 14.04 64bit – fix
- xubuntu 12.10 probleme de son avec VLC – pulse audio – alsa – toshiba L855D – solution
- Evolution sous xubuntu 12.10 – bug affichage a la configuration – solution temporaire
- Booster son acces internet en changeant de DNS pour opendns
- Serveur DLNA sous ubuntu – minidlna
- sshfs sous windows – dokan sshfs
- xubuntu 11.10 Installer le plugin java pour firefox
- Installer Google Earth sur Xubuntu 11.10
- Installer nagios sur Fedora 11 depuis les sources



Wow, after multiple tries and reading blog after blog, your tutorial actually worked. Thank you. I appreciate it.
Is it possible you can show how to get the web page for pi-hole to work instead of disabling it?
thanks!
During the installation process, just pick the « On » option for web interface.
You can try to run pihole -d (diagnostic and see the options ) : https://discourse.pi-hole.net/t/no-web-interface-after-install/157/3
And most likely this would do (setup lighttpd and copy config files, but I did not try it) : https://wiki.archlinux.org/index.php/Pi-hole#Set-up_lighttpd
Thanks.
When I choose web admin on install, the DNS and FTL service no longer are running and will not start. Tried to add Admin page to fresh install but would not work. Tried fresh install on Ubuntu 20, everything installed fine, all services up and running, but web page would not come up.
Diag shows gateway not responding.