GNU – Linux
5G network hosted in the cloud, no internet, no phone ! So smart ! And I ended on TV, This week in cyber
Yes, someone smart thought that it was a good idea to put the 5G management platform in the cloud, so we are making is super easy for foreign actors, already targeting the big cloud players, to fully disrupt the country communication capabilities, just by taking down one infrastructure.
It seems that common sense jumped from the boat a while ago, where the shiny goal of integral communication spying made them forget the first goal of communication infrastructure, ensuring resilience and coordination in case of incident.
When the cloud fall, you won’t be able to call for support, because phone networks will fall with it. My 2 cents.
Side note, don’t forget to follow VARS Corporation as well, I do share some intelligence on it, along with the team, …. yes half of the posts in French, but hey, don’t you enjoy my french accent ?!
Another note, I had my first TV News apparition this week, in Quebec, in French, and that was cool ! Alex on TV looks like this (oh boy, I was stressed ) :
Now, this week in 63 points, for you to remain aware as usual :
1 – James W from the FBI shared a great list for you to opt out from people tracking search engines ! Fast And The Furious: Opting Out Of People Search Engines, Privacy And Digital Exhaust
2 – There is a festival of infected NPM repos lately ! Malware Discovered in Popular NPM Package, ua-parser-js
3 – Skimmer injected on the site and more than 32k persons impacted- SCUF Gaming store hacked; Customer data exposed
4 – Do not take the data if you can’t protect it, like the cloud pretty much – Criminal Hacker sells the data for millions of Moscow drivers for $800
5 – When you go on youporn using private browsing, your ISP sees it all, and does resell all this info to whoever is willing to pay for it – FTC: ISPs collect and monetize far more user data than you’d think
6 – Hacked criminal hackers ! Feds Reportedly Hacked REvil Ransomware Group and Forced it Offline , but, soon after, the group claimed it was only a small part of the « sub contractors »…
7 – Cyber conflict being more politic it seems. Their main goal was money, some in there were state sponsored spying, but now a call to action against the US. We’ll see, not sure there is any real coordination between challengers in crime. Groove ransomware calls on all extortion gangs to attack US interests
8 – CISCO patch time – Cisco SD-WAN Security Bug Allows Root Code Execution
9 – The power of the cloud, 24/7 spying. And yet people pay to place 24/7 spying devices, bugging their homes themselves. I found an Amazon folder with thousands of audio recordings from my home gadgets
10 – Interesting review of previous incident, most likely caused by nature, but, showing the potential impact of the same failure triggered by a cyber attack. When Cyber Mimics Nature – How Cyber Attacks Can Cause Global Environmental Catastrophes.
11 – Never pay ransom, don’t finance crime, and report to law enforcement, they might have a decryptor, so do it right – BlackMatter ransomware victims quietly helped using secret decryptor
12 – The cloud will be destroyed, I hope your DRP (disaster recovery plan), and risk register have considered this. SolarWinds hackers are going after cloud, managed and IT service providers.
13 – It’s discourse patch time ! CISA urges admins to patch critical Discourse code execution bug.
14 – How do you reduce your attack surface ? Hackers Exploited Popular BillQuick Billing Software to Deploy Ransomware
15 – You are hacked, I’m hacked, question is, how much of you was on this device ? NYT Journalist Repeatedly Hacked with Pegasus after Reporting on Saudi Arabia
16 – AI is also powering madness – Despite spending millions on bot mitigation, 64% of organizations lost revenue due to bot attacks
17 – The truth comes out, as often in the big tech world, deception is king, abuses and betrayals, in an unlimited rush toward money. Explainer: What are the Facebook Papers?
18 – The ICT and industrial security podcast interestingly start to speak about patching automation. Automating vulnerability handling – a promising new standard: CSAF | Episode 70
19 – You can’t play with your security posture ! It goes bad. CONTI now positionnned as client access service broker ! Encrypting, stealing, and selling access to your network !
20 – In your browser, the more add-on you install, the bigger your supply chain is, and the bigger your attack surface is. Mozilla blocks malicious add-ons installed by 455K Firefox users
21 – Don’t fall for the scam ! FOMO (fear of missing out) will get you hacked or trapped – Millions of Android users targeted in subscription fraud campaign
22 – Australia, what are you doing ?!! Australia drafts Online Privacy Bill to bolster data security – Sounds right, except they scoped applicability to almost nothing !
23 – We should assume anyway nowadays that the network is no longer the perimeter, at least the wireless network, and security must be embedded in endpoint from an enterprise standpoint – Wardrivers Can Still Easily Crack 70% of WiFi Passwords
24 – No attacker said ever « this is out of scope » – Gas Stations in Iran Downed by Cyberattack
25 – EMOTET reborn as Squirrelwaffle – Spammers use Squirrelwaffle malware to drop Cobalt Strike – I remember by then using Squirrelmail webmail, it was so quite, but here, despite a terrific breakfast stealer name, squirrelwaffle doesn’t taste very good !
26 – Threat actors are really focusing on cloud providers and IT service providers – Lazarus Attackers Turn to the IT Supply Chain
27 – Patch management of your WordPress site and plugins is critical – Brutal WordPress plugin bug allows subscribers to wipe sites
28 – One less, already something. Other marketplaces will certainly see a surge in traffic – DoJ & Europol Arrest 150 in Disruption of DarkNet Drug Operation
29 – US federal investigators today raided the Fla. offices of PAX Technology, a Chinese provider of point-of-sale devices – Front shop takedown. Know your enemies.
30 – Turn off connectivity if you don’t need it ! Protect your device from both security and privacy standpoint – Tracking Mobile Devices by Analyzing Bluetooth Transmissions
31 – Always verify and then trust, each time – Attackers Hijack Craigslist Emails to Bypass Security, Deliver Malware
32 – Will your security controls be effective against such attacks ? FBI: Ranzy Locker ransomware hit at least 30 US companies this year
33 – Never properly understood, the cloud shared responsibility model is still an issue leading to major cloud abuses and privacy issues – Public Clouds & Shared Responsibility: Lessons from Vulnerability Disclosure
34 – Aside of following me on linkedin : « Top 13 Can’t-Miss Cybersecurity Awareness Tips«
35 – Security posture must be adjusted to your threats. You must have MFA everywhere, and using authenticator apps will be good for you. Twitter employees required to use security keys after 2020 hack.
36 – it’s apple patch time again ! (if you haven’t already) – Apple Patches Critical iOS Bugs; One Under Attack
37 – Babuk decryption key available – Babuk ransomware decryptor released to recover files for free
38 – Supply chain risk management at country level is tricky. Especially when most of your products are made in China – US bans China Telecom Americas over national security risks
39 – it’s an NPM supply chain infection festival lately ! Malicious NPM libraries install ransomware, password stealer
40 – Highly regulated, the specifics of this verticals raise interesting challenges – SECURITY INTELLIGENCE REPORT – CISO Point of View : Analysis of Storage & Backup Security in the Financial Services & Banking Sector
41 – Another decryptor available ! Free decryptor released for Atom Silo and LockFile ransomware
42 – it’s adobe patch time once again – Adobe’s Surprise Security Bulletin Dominated by Critical Patches
43 – The so called « grief » ransomware group published some sample content of claimed to be internal NRA files – Russian Ransomware Gang Claims to Have Hacked the NRA
44 – Well put about how to handle ransomware situation – You’ve Just Been Ransomed … Now What?
45 – The cloud is infected and this new threat comes with official apps ! New AbstractEmu malware roots Android devices, evades detection – Comes from the so protected playprotect supposedly cloud protected stuff.
46 – The cloud is infected and it poisons Internet, or vice versa, anyhow, you can’t trust anything you see online without due diligence first – Ransomware gangs use SEO poisoning to infect visitors
47 – A free pass to COVID ? sounds exciting no ? EU investigating leak of private key used to forge Covid passes
48 – but, but, but, butt cloud leaked again ! PII feist ! Sensitive data of 400,000 German students exposed by API flaw
49 – Undetected so far, in memory malware, talking with C2C and loading needed remote modules – New Wslink Malware Loader Runs as a Server and Executes Modules in Memory
50 – Algorithms are not the only problem of social media, people are a big one too – Facebook Removed The News Feed Algorithm In An Experiment. Then It Gave Up (now weirdly called Meta)
51 – spyware patch time – Emergency Google Chrome update fixes zero-days used in attacks
52 – Nothing new, everything connected is a target – All Sectors Are Now Prey as Cyber Threats Expand Targeting
53 – A first step toward security by design – Top Hardware Weaknesses List Debuts
54 – Privileges escalation, means that this can only be exploited after the initial access phase – All Windows versions impacted by new LPE zero-day vulnerability
55 – Very interesting, Amazon seems to reach a limit and benefits are collapsing. Unexpected – Amazon delivers big earnings miss, Jassy warns Q4 will bring ‘several billion dollars of additional costs’
56 – connected=hacked – Critical Polygon Blockchain Vulnerability Could Allow Withdrawing Huge Amounts
57 – The less apps you install, the smaller the attack surface, the safer you are – Android spyware spreading as antivirus software in Japan
58 – Yet another WordPress plugin vulnerability – WordPress plugin bug impacts 1M sites, allows malicious redirects
59 – Microsoft decided to eliminate all challengers on any field by taking 100% control over any features requiring third party – Microsoft: Windows web content filtering now generally available
60 – Cloud dependency is awful – Google Chromebooks failing to enroll due to network issue
61 – Moving toward cloud systems – Hive ransomware now encrypts Linux and FreeBSD systems
62 – Use the details of this article as threat intelligence and understand how crime operates – Police arrest hackers behind over 1,800 ransomware attacks
63 – Season scams are always around – What’s the Phishing Scam Equivalent of Your Favorite Halloween Costume?
BTW, I always link to LinkedIn article shares, because I usually add a lot of complementary links in comments allowing to get better coverage.
That would be about it ! Have a good weekend all !
![]()
Migrating an old WordPress and handling character set, UTF8, latin1, latin1_swedish_ci
Sharing a quick one because it took some research for me to figure this one, not too long, but I don’t have to search again :D
Basically, old WordPress from years ago, were using default character set called « latin1_swedish_ci » as default collation name, latin1 in short.
When you must migrate to a newer system because you were running an old CentOs which is no longer supported, and you start to migrate to a Debian based machine, the new default is UTF8.
So you backup your WordPress, (and ideally you used a dedicated machine for the database, so as you can have more flexibility in your workloads and yet can still backup the full DB server), and you restore it on your new server (a big tar.gz of you site content that you copied with scp by example).
You’ll have to fix all the glitches linked to PHP version change, sometimes the front end won’t work, but the admin page of your WordPress should still load. Web server logs will tell you what is wrong (a theme in my case was using functions that were no longer supported). If you can’t even get to the admin page, wp command line utility should help you update the instance from command line (another topic)
Anyway, while you log in the admin section, you will have to apply updates (as you could not on the old system, stuck with an older PHP version and other libs).
Suddenly you realize that all the accents (yes, French content and more) are totally messed up ! Yes, on the new server, everything is assumed by default to be UTF8 !
So you need to figure out what was the previous encoding of your content in the database.
You have to log on your mysql / mariadb server, as root of mysql and run the following command :
SELECT * FROM information_schema.SCHEMATA;
This will show up all your databases and their actual default character set name and default collation name !
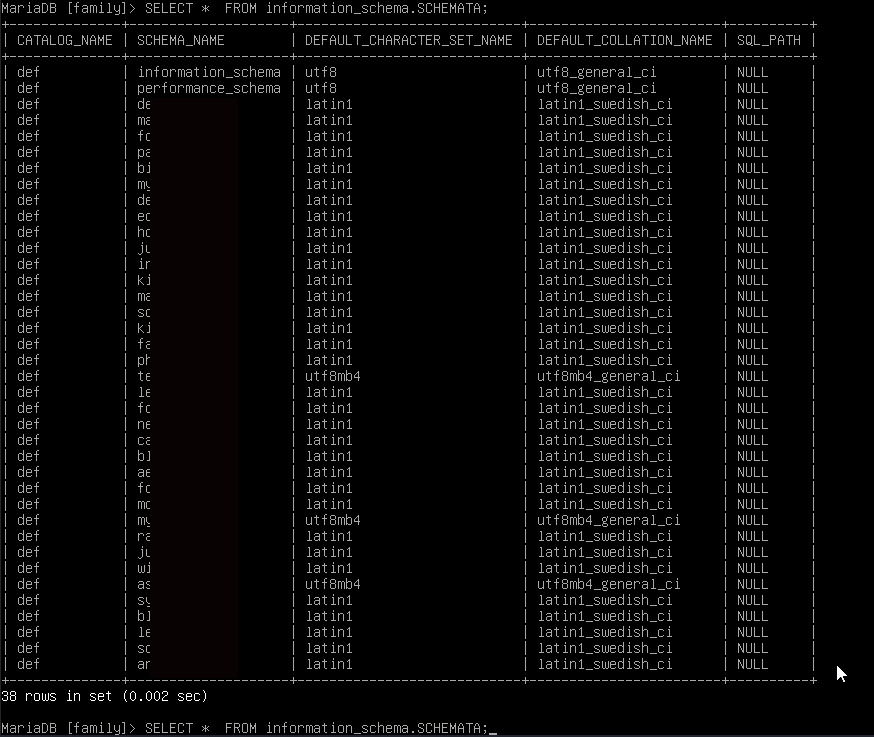
As you can see, a lot of my old sites and databases are in latin1.
Because your WordPress has been updated, the wp-config.php file doesn’t contain all the new options, and it uses the default, including the charset default. In my case UTF8 in the new version, but as you can see, my data is in latin1 encoding.
So the fix was to add in the wp-config.php the DB_CHARSET value, to match with the database :
define ('DB_CHARSET', 'latin1');
Once you did this, all your accents and special chars should display properly !
Memo for myself mainly, but maybe it will help others.
![]()
From a broken TLS CA, to Facebook, to FIN12 hit and run
Yet another crazy week in cyber, which makes me wonder if there is any quiet week anymore, and, as a lot spoke about mental health as well, how long do you think a human can take all of this ?
Meanwhile, I’m still motivated to do good, and while ransomware gangs make millions every month, we try to get a couple of bucks from people so as we can help secure them (not asking for money, just tough to get organization to spend just enough to protect themselves).
But I’m telling you, this won’t last, ransomware projections are so huge, that we’ll come to a point where, sorry, we don’t take new customers. Scarcity, is where we’re heading, and I’m telling you, find your cyber security partner NOW, because we, skilled humans in this field, are in very limited supply. The illusion of the market may make you think you have choice, but there is a fun fact in the back end, A sells the skills of B, which sells the skills of C, which rely on A for any overflow…… do you see it coming ?
Meanwhile, Monica and myself are going to share some insights on our CISO experience, hopefully a series to start in November, and well scheduled (according to her, she likes when things are organized, and it’s good !), and pretty fun (according to me, and her actually, we agree on this)…. (wait, did I mean we don’t agree on everything ? )…. (seems I’m talking to myself now…. ok, let’s move on).
Edit : Monica said that I should say that the audience will have an AWESOME opportunity not only to ask ya questions for this episode but ALSO TO SHAPE OUR NEXT EPISODES and what challenges we address (that’s what she said :P )
This week as well, did record a 6 min LinkedIn podcast with Mani Keerthi which actually turned to be very relevant in a pretty short time ! Thanks Mani ! :)
And now, finally, this week in 56 points :
1 – Letsencrypt updated their CA (certificate authority) and it went bad for a lot of stuffs – Let’s Encrypt’s root certificate has expired and stuff is breaking all over the place
2 – Surprise, yet another massive leak – US retailer Neiman Marcus confirms Data breach – Just 4.6 Millions customers data
3 – You first need to have proper security posture, otherwise, nothing will help you – US unites 30 countries to disrupt global ransomware attacks
4 – I fixed the issue by dropping any phone call. Only accepting known persons over encrypted channels – FCC orders phone carriers to enforce unlawful robocall blocking
5 – Hacked down to hardware – Flaw in AMD Platform Security Processor Affects Millions of Computers
6 – Cryptoland never cease to amaze me – Crypto platform mistakenly gives $90M to users, asks for refund
7 – Just a reminder, building your security posture, assessing the potential impact and placing proper security controls to mitigate the risk is not optional, unless you absolutely don’t care – Sandhills online machinery markets shut down by ransomware attack
8 – That’s hacking ! The power of technical creativity ! Creating Wireless Signals with Ethernet Cable to Steal Data from Air-Gapped Systems
9 – Clowd style leak ! Poorly Configured Apache Airflow Instances Leak Credentials for Popular Services
10 – Like it or not, patch management is critical – New Atom Silo ransomware targets vulnerable Confluence servers
11 – Good work Europol, some less criminals – Ransomware operators behind hundreds of attacks arrested in Ukraine (doesn’t calm down anyhow, but that’s already something ! )
12 – Learn why privacy and data protection is important (aside of Pandora papers ) – Transnational fraud ring stole millions from Army members, veterans
13 – Quite an interesting take on this one, after all we are in a continuously evolving environment, seeing rising threats, and regulation playing ketchup – Regulations & Ransomware: A Quick Overview
14 – Facebook offline day ! Great for humans mental health, on this linkedin post, I covered, including comment, the whole story, with other, pointing to the BGP error , but we all know the truth : The home router of Mark got powered off as his cat stepped on it, and poof ! Facebook Blames Outage on Faulty Router Configuration
15 – Just don’t SMS, anything you type on it, is being reviewed by thousands of people, indexed, reshared and all – Company That Routes Billions of Text Messages Quietly Says It Was Hacked
16 – Android patch time ! Android October patch fixes three critical bugs, 41 flaws in total
17 – You are hacked ! UEFI (aka BIOS) hacked since 2012 – New UEFI bootkit used to backdoor Windows devices since 2012
18 – Not even out for a day, already broke network support for widely used Intel network/wifi cards – Microsoft confirms Windows 11 issues with VirtualBox, Intel Killer
19 – Do you have accounts without MFA ? unacceptable – Large ransom demands and password-guessing attacks escalate
20 – Almost forgot ! I was on 123CMMC with the awesome Dana Mantilia ! We had a great episode on here :
21 – it’s apache web server patch time ! Apache fixes actively exploited zero-day vulnerability, patch now
22 – It smells a lot like….clowd ! The Telegraph exposes 10 TB database with subscriber info
23 – Root cause is credentials guessing or Brut force, so don’t expose your management networks and have decent governance – Ransomware gang encrypts VMware ESXi servers with Python script
24 – Very positive outcome, some souls got saved from evil thanks to this failure – Facebook outage leads to massive user exodus to Telegram, Signal
25 – You should already know this but a reminder – 3 Ways the Government Can Track Your Phone
26 – Don’t forget, private browsing still allows your Internet Service Provider to see everything you do. Private browsing only protects you if someone looks at your browsing history. Firefox improves advertising tracker blocking in private browsing
27 – Take this as an example ! YOU must do it too on all your accounts – Google to turn on 2-factor authentication by default for 150 million users
28 – Good move, especially that investing less than the payment made to criminals is enough to build your whole security posture and strongly reduce the likelihood of such incident and totally squeeze the potential impact – Ransom Disclosure Act would give victims 48 hours to report payments
29 – Adam will never find a job in IT ever again – Fired IT admin revenge-hacks school by wiping data, changing passwords
30 – The Internet of threats (IoT) and the Industrial Internet of Threats (IIoT), must be sandboxed and protected behind layered defense and zero trust network access control – Multiple Critical Flaws Discovered in Honeywell Experion PKS and ACE Controllers
31 – Fact is, you need MFA at the very least, and, you should think security architecture with additional controls, such as « geo fencing », and more, capabilities depending. ATO (account take over) attacks increased 307% between 2019 and 2021
32 – The cloud leaks again, I think there might be a medication for this, I mean it can’t hold anything, anything it eats just is spread around…. looks like the cloud is sick to me. The entirety of Twitch has reportedly been leaked, Source codes and user payouts among the data released in a 128GB torrent
33 – All these connected crap will get you killed ! STOP connecting everything, this is absolute non sense ! Medtronic urgently recalls insulin pump controllers over hacking concerns
34 – The cloud is a tool, powerful, sensitive and dangerous, that criminals masters ! Iranian Hackers Abuse Dropbox in Cyberattacks Against Aerospace and Telecom Firms
35 – Backups are only a corrective measure, it means, it’s the ultimate resource you should nod need for recovery – CISO Point Of View ‘Mashup’: The Importance of Securing Storage & Backup
36 – You are hacked, you just don’t know it yet ! This malware is active since 2018 ! Criminal Hackers use stealthy ShellClient malware on aerospace, telco firms
37 – Good move, but, now that Pandora box is open, I’m afraid it’s too late – European Parliament calls for ban on AI-powered mass surveillance
38 – Challenging times ahead. We know compliance doesn’t equal security, but, self regulation has proven to be ineffective – New Regulations Are Coming — Get a Handle on Your App Portfolio
39 – There is no such thing as free lunch ! Firefox now shows ads as sponsored address bar suggestions
40 – Diversity is critical to ensure resilience. Monoculture is lethal everywhere – Netherlands orders Apple to offer more App Store payment methods
41 – No comment – Microsoft fixes bug blocking Azure Virtual Desktops security updates
42 – How do you like your Yamale ? Some like it hot, hot yamale ! Snake yamale ! Code Execution Bug Affects Yamale Python Package — Used by Over 200 Projects
43 – Full unauthenticated remote access, anybody can watch your b…eer – Unpatched Dahua cams vulnerable to unauthenticated remote access
44 – A good reading about pentest on your (not actually yours, but ok) AWS stack – Penetration Testing Your AWS Environment – A CTO’s Guide
45 – If you self host an onionshare instance, make sure you patch – Serious Data Exposure Vulnerabilities Spotted In OnionShare Platform
46 – Good move, no longer have to guess editor’s website, find terms and conditions and discover how to unsubscribe – Apple now requires all apps to make it easy for users to delete their accounts
47 – I don’t take calls anymore except through encrypted channels – Fraudulent robocalls to cost consumers $40 billion in 2022
48 – Cut the BS and do it right or don’t do it ! U.S. govt to sue contractors who hide breach incidents
49 – A good reading about these ICS affected by vulnerabilities – Four Critical Vulnerabilities Discovered in Bosch Rexroth WEB Interfaces
50 – An apache patch patching the patched apache as it didn’t patch patchingly ! Apache emergency update fixes incomplete patch for exploited bug
51 – Automated detection and response is mandatory ! No time, the only time you have is the time to be encrypted ! FIN12 hits healthcare with quick and focused ransomware attacks
52 – How would your organization detect and respond to such incident ?
What is your RPO ? Recovery Point Objective define how much data you’ll lose between last valid and tested backup, and restore time.
What is your RTO ? Recovery Time Objective defines how long it will take for you to recover – Engineering giant Weir Group hit by ransomware attack
53 – Attribution is always a tricky game. Proxy, fork anyone ? But for sure, it’s easier to have visibility when you collect telemetry (backdoor) from most of the computers in the world ;) Microsoft: Russian state hackers behind 53% of attacks on US govt agencies
54 – hard coded credentials + cloud is a recipe for disaster :) leak accelerator :) BrewDog exposed data for over 200,000 shareholders and customers
55 – Rootkit active for 18 months, just spotted now – Researchers Warn of FontOnLake Rootkit Malware Targeting Linux Systems
56 – All your eggs in the same basket ! Monoculture and Market Share: The State of Communications
and Collaboration Software in the US Government
And that’s about it for this week, good enough I guess !
Have a good weekend all ! See you on here hopefully next week !
Alexandre Blanc Cyber Security
![]()
Links
Calendrier
| L | M | M | J | V | S | D |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | ||||
| 4 | 5 | 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 | 16 | 17 |
| 18 | 19 | 20 | 21 | 22 | 23 | 24 |
| 25 | 26 | 27 | 28 | 29 | 30 | 31 |
Recherche
Derniers articles
Tresronours Twitter
Keywords cloud topic
Membre de la FSF
Liens qui vont bien
Mots clés vrac – keyword cloud
License du contenu – CC By NC SA
Archives
- Getting voLTE on your Android with Fizz and others
- Defining the scope of an ISMS within ISO 27001
- Resumed posting and expanding on X
- Linkedin Access to your account has been restricted – Final debrief and resilience plan
- I’m thankful for the support I get in rough time
- Cyber security news of the day – 2024 May 31
- Alexandre Blanc Cyber Kicked out from Linkedin
- You’ll most likely find me on LinkedIn
- The Russian roulette landing page !
- RTSP, Debian, VLC, not playing, IP Camera
- 5G network hosted in the cloud, no internet, no phone ! So smart ! And I ended on TV, This week in cyber
- They lock the door for privacy… but they keep a copy of the key, and couple of backdoors
- Worst is yet to come, but they all warned you
- Migrating an old WordPress and handling character set, UTF8, latin1, latin1_swedish_ci
- From a broken TLS CA, to Facebook, to FIN12 hit and run
- Yes we can fix this mess, but do we want to ? That’s another story
- Criminals are still dominating the game, why are we doing so wrong, and what can we learn in this tech ocean ?
- Riding cloud can be tricky, don’t fall from it, in the weekly cyber !
- The threat landscape is very dynamic – Cyber news this week
- Cybersecurity is not obvious even for this newsletter !
- Install Slack desktop app on Kali rolling fixing libappindicator3-1 missing dependency
- How to delete all resources in azure to avoid charges after trial on your forced credit card registration
- Proxmox – ZFS – Dead drive on active VM, recover from replicated disk
- Restrict access to proxmox web admin interface
- Migrate your ESXI VMs to proxmox ZFS
- Install your VPN server with pi-hole on OVH VPS in 30 min
- Using raspberry pi 3 as wifi bridge and repeater and firewall
- Raspberry 3 – create a wifi repeater with USB wifi dongle
- raspberry 3 – routeur pare feu point d’acces wifi avec filtrage pub et tracking – router firewall access point with ads and tracking filtering
- Dell XPS 13 touchpad – corriger la sensibilité
- Utiliser Zazeen set top box depuis une connexion videotron
- Fermeture de mon compte facebook – la dernière goutte
- Choisir un kernel par defaut au demarrage de Centos 7.2 – configuration grub2
- Openvpn access server 2.0.25 et android
- Régler la luminosité du laptop par ligne de commande
- chromium outlook web app version complete sous linux
- Nexus 7 2012 – android 5 lollipop solution au probleme de lenteur
- HDD led sur Xubuntu – xfce
- xubuntu 14.04 verrouiller ecran de veille et desactiver mise en veille a la fermeture de l’ecran
- Authentification avec Radmin en utilisant Wine sur Gentoo
- Patcher bash sur une distribution plus supportee comme fedora 11
- Zimbra desktop sous xubuntu 14.04 64bit – fix
- xubuntu 12.10 probleme de son avec VLC – pulse audio – alsa – toshiba L855D – solution
- Evolution sous xubuntu 12.10 – bug affichage a la configuration – solution temporaire
- Booster son acces internet en changeant de DNS pour opendns
- Serveur DLNA sous ubuntu – minidlna
- sshfs sous windows – dokan sshfs
- xubuntu 11.10 Installer le plugin java pour firefox
- Installer Google Earth sur Xubuntu 11.10
- Installer nagios sur Fedora 11 depuis les sources







